Search for "Jason" returned 222 results
63 min
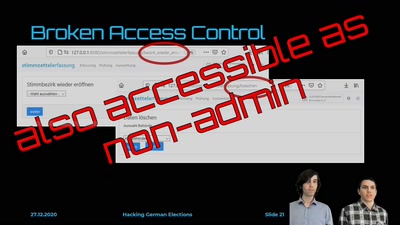
Hacking German Elections
Insecure Electronic Vote Counting - How It Returned and Why…
32 min
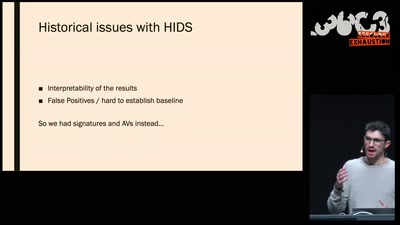
The Case for Scale in Cyber Security
Security Track Keynote
56 min
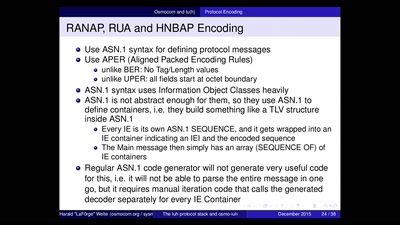
Running your own 3G/3.5G network
OpenBSC reloaded

43 min
How Facebook tracks you on Android
(even if you don’t have a Facebook account)
62 min
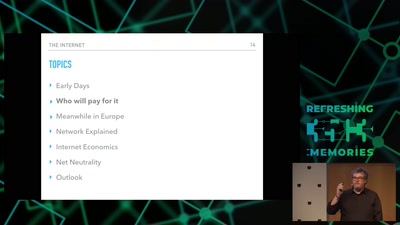
Internet, the Business Side
a try to explain the ecosystem

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
63 min
Das nützlich-unbedenklich Spektrum
Können wir Software bauen, die nützlich /und/ unbedenklich…

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
62 min
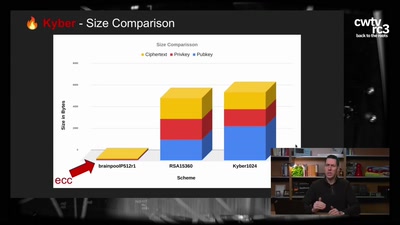
Kyber and Post-Quantum Crypto
How does it work?
60 min