Search for "mel" returned 2579 results
29 min
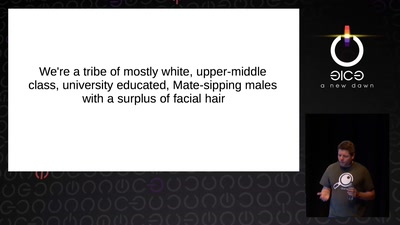
Infocalypse now: P0wning stuff is not enough
Several failure modes of the hacker scene
57 min
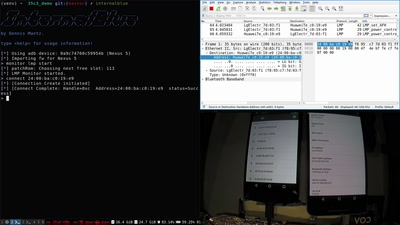
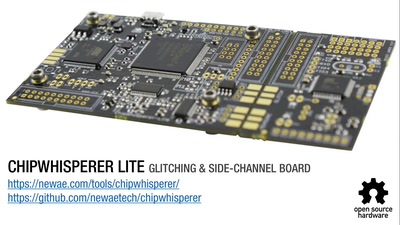
TrustZone-M(eh): Breaking ARMv8-M's security
Hardware attacks on the latest generation of ARM Cortex-M…
58 min
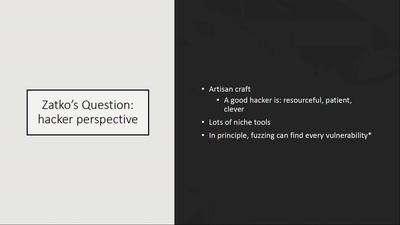
How risky is the software you use?
CITL: Quantitative, Comparable Software Risk Reporting

61 min
"The" Social Credit System
Why It's Both Better and Worse Than We can Imagine
62 min
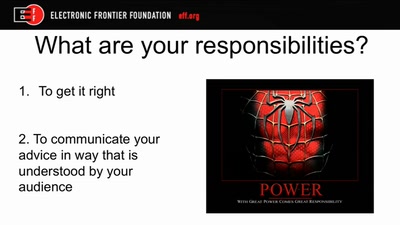
The Internet (Doesn't) Need Another Security Guide
Creating Internet Privacy and Security Resources That Don't…
49 min
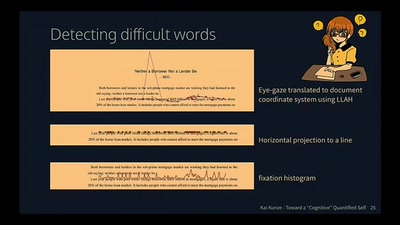
Toward a Cognitive "Quantified Self"
Activity Recognition for the Mind
56 min
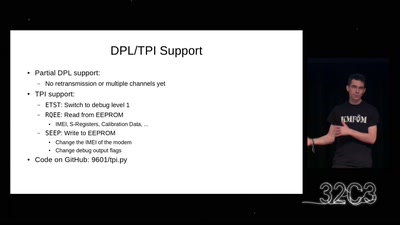
Iridium Update
more than just pagers
38 min
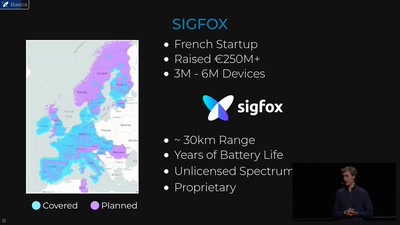
Hunting the Sigfox: Wireless IoT Network Security
Dissecting the radio protocol of Sigfox, the global…
60 min
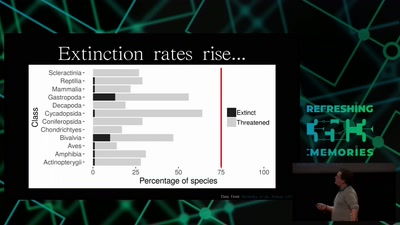
Hacking Ecology
How Data Scientists can help to avoid a sixth global…

40 min
Boiling Mind
Analysing the link between audience physiology and…
69 min
cryptocurrencies, smart contracts, etc.: revolutionary tech?
short answer: Yes!
60 min