Search for "fh" returned 2458 results
40 min
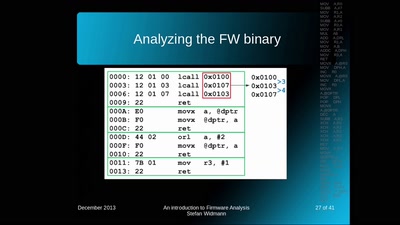
An introduction to Firmware Analysis
Techniques - Tools - Tricks
32 min
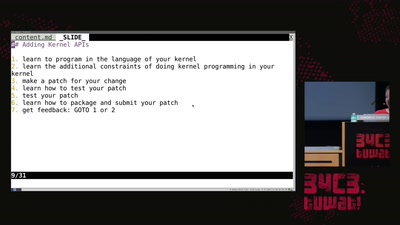
library operating systems
reject the default reality^W abstractions and substitute…
60 min
Why is GPG "damn near unusable"?
An overview of usable security research
58 min
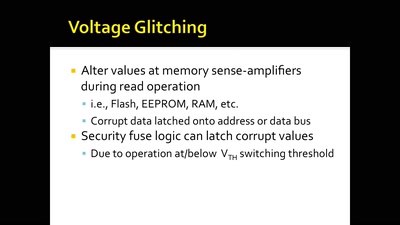
Glitching For n00bs
A Journey to Coax Out Chips' Inner Secrets
60 min
Lets break modern binary code obfuscation
A semantics based approach
62 min
radare demystified
after 1.0
60 min
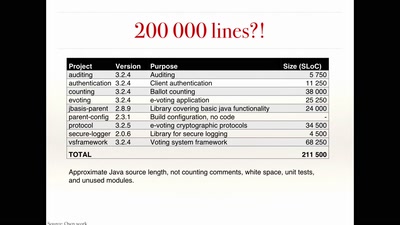
The rise and fall of Internet voting in Norway
Evaluating a complex cryptographic implementation

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities

63 min
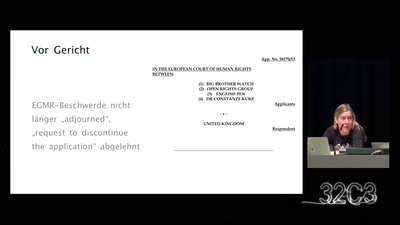
Das Assange-Auslieferungsverfahren
Als Prozessbeobachter in London

54 min
A la recherche de l'information perdue
some technofeminist reflections on Wikileaks
60 min
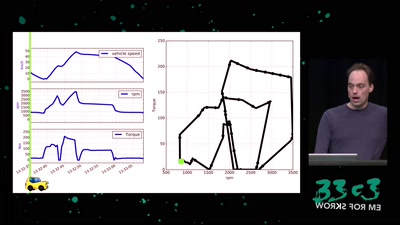
Software Defined Emissions
A hacker’s review of Dieselgate
62 min
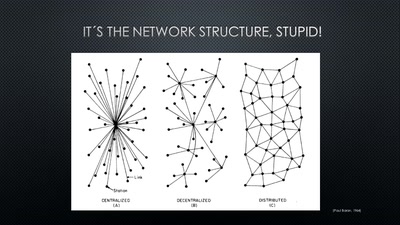
A New Kid on the Block
Conditions for a Successful Market Entry of Decentralized…
39 min
ID Cards in China: Your Worst Nightmare
In China Your ID Card Knows Everything
60 min
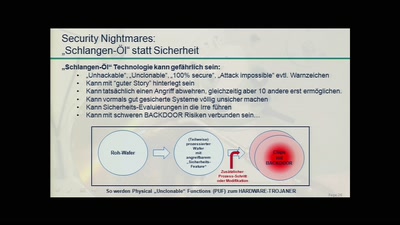
So you want to build a satellite?
How hard can it be? An introduction into CubeSat development
61 min
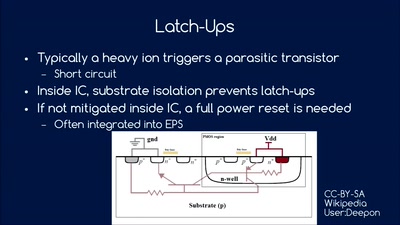
25 Jahre Chipkarten-Angriffe
Von der Historie zur Zukunft
62 min