Search for "JO" returned 10386 results
56 min
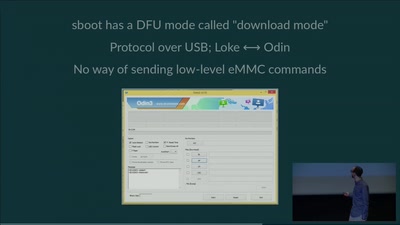
eMMC hacking, or: how I fixed long-dead Galaxy S3 phones
A journey on how to fix broken proprietary hardware by…
74 min
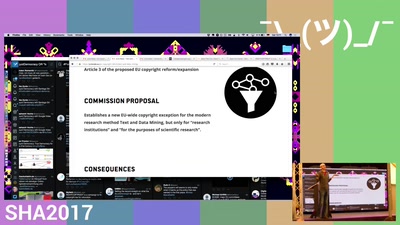
Let's stop EU copyright expansion
If you like untaxed links and unsurveilled uploads, you…

78 min
Stealth malware - can good guys win?
Challenges in detecting system compromises and why we’re so…
29 min
The Pirate Cinema
Creating mash-up movies by hidden activity and geography of…
40 min
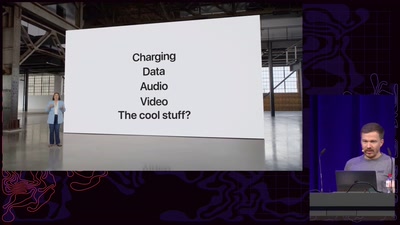
ACE up the sleeve:
Hacking into Apple's new USB-C Controller
26 min
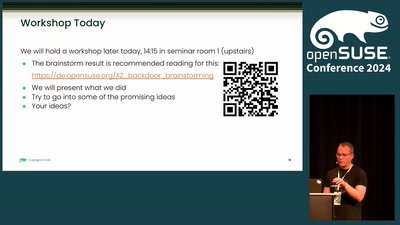
The XZ Backdoor - report from our side, retrospection and looking forward
supply chain challenges

61 min
PyPy - the new Python implementation on the block
Language/VM R&D, whole program type inference, translation…
56 min
The importance of resisting Excessive Government Surveillance
Join me in exposing and challenging the constant violations…
50 min
Inclusive Design
Wie man das Leben von Menschen verbessern kann, indem man…
42 min
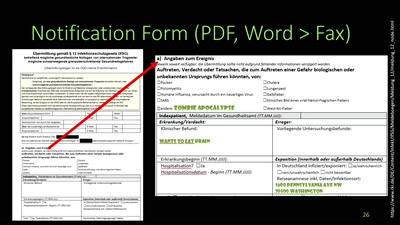
Zombie Apocalypse vs. International Health Regulations
Introducing a very important piece of international law and…
37 min
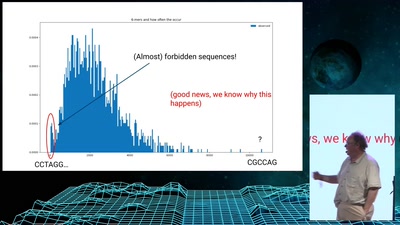
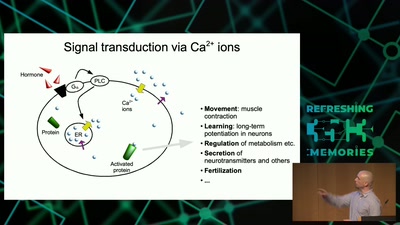
Information Biology - Investigating the information flow in living systems
From cells to dynamic models of biochemical pathways and …
70 min
coreboot: Adding support for a system near you
Working with the open source BIOS replacement and getting a…

66 min
COMPLETE Hard Disk Encryption with FreeBSD
Learn how to effectively protect not only your data but…
48 min
10 Years of Fun with Embedded Devices
How OpenWrt evolved from a WRT54G firmware to an universal…
43 min
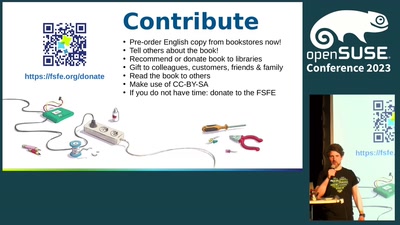
Ada & Zangemann - A Tale of Software, Skateboards, and Raspberry Ice Cream
A modern fairy tale that conveys the joy of tinkering and…
41 min
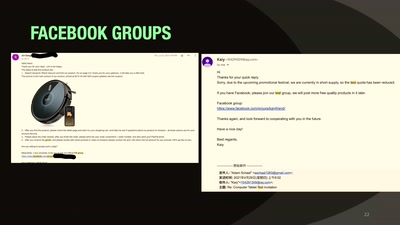
Our Time in a Product Review Cabal
And the malware and backdoors that came with it.

36 min