Search for "Mo" returned 10422 results
29 min
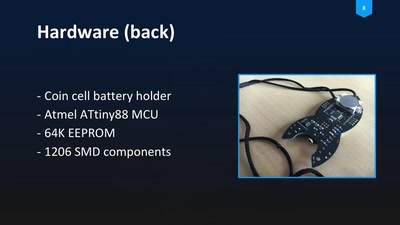
Blinkenrocket!
How to make a community project fly
25 min
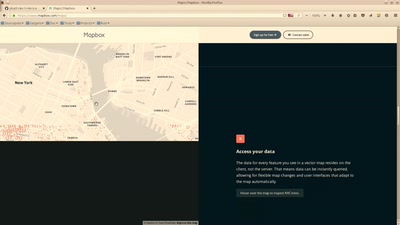
Von WMS zu WMTS zu Vektor-Tiles
Eigene Daten als MB Vektor-Tiles publizieren
30 min
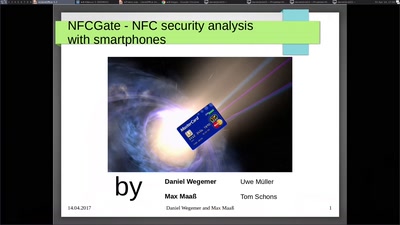
NFCGate - NFC security analysis with smartphones
Use your smartphone to relay NFC data
48 min
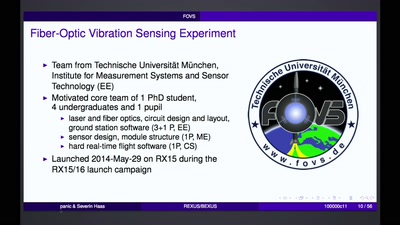
REXUS/BEXUS - Rocket and Balloon Experiments for University Students
How to bring student experiments into space.

61 min
The Realtime Podcast
Everything you need to know about Podcasting

51 min
EFI Rootkits
Abusing your Firmware to backdoor the kernel
38 min
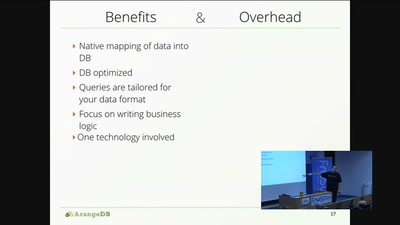
Multi-Model NoSQL Databases
An introduction to Polyglot persistence and NoSQL
24 min
Security alerting made easy using Python
Sending real-time notifications to Discord and other…
27 min
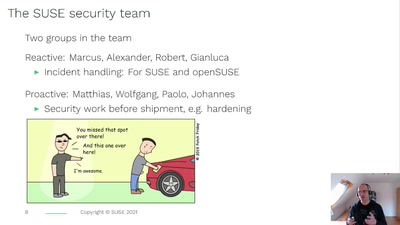
*sing* %post and %pre and securiteeee
How not to get a CVE assigned while packaging
54 min
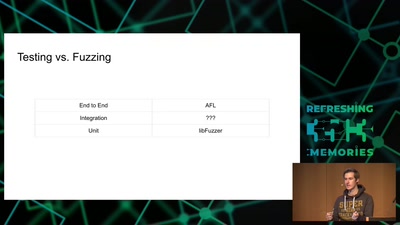
Attacking Chrome IPC
Reliably finding bugs to escape the Chrome sandbox
37 min
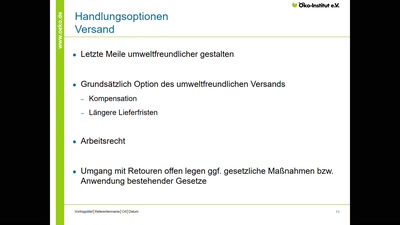
E-Commerce – Greening the Mainstream
Wie können Amazon & Co. ökologischer und sozialer werden?
20 min
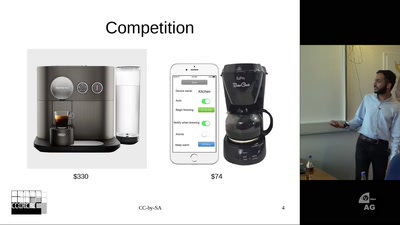
HTCPCP - Networking your Coffeepot
IoT done right for fun and no profit

41 min
privacyIDEA
Die Open Source Alternative zu RSA SecurID & Co.
43 min
Artist Talk
We Show You What You Want To See
50 min
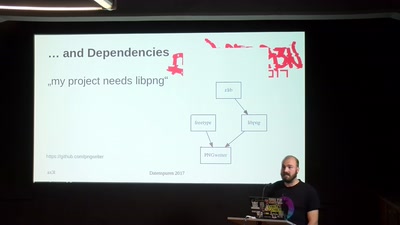
Modern Software Packaging for Developers
Wait, how to install your FOSS project again?
35 min
Weaponized Social
Understanding and tools to mitigate network-scale violences
20 min
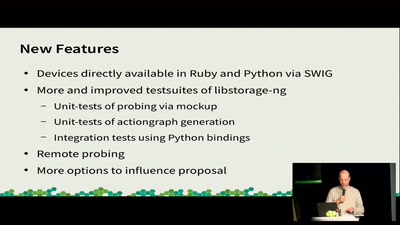
Next Generation Storage for YaST
Why Users should look forward to the Redesign.

30 min
Closing Event
So long and thanks for all the fish
48 min
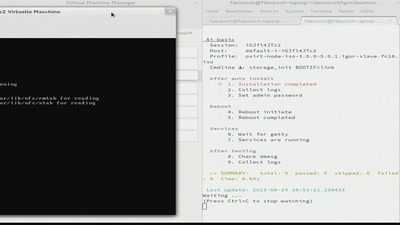
Testing a LiveCD? Igor is doing it.
or: How to make testing a distribution fun.
62 min
Public Library/Memory of the World
Access to knowledge for every member of society
28 min
Hardware attacks: hacking chips on the (very) cheap
How to retrieve secret keys without going bankrupt
62 min