Search for "Mo" returned 10605 results
17 min
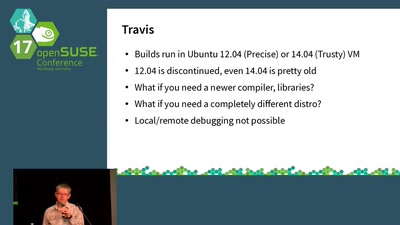
Continuous Integration using Travis and Docker
There is no excuse for NOT using continuous integration
29 min
Open vSwitch and DPDK - Your VMs deserve better
Using OvS + DPDK to boost inter-VM network traffic

59 min
10GE monitoring live!
How to find that special one out of millions
53 min
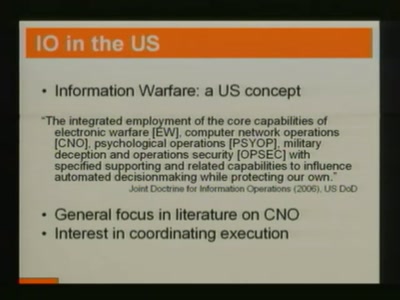
Crouching Powerpoint, Hidden Trojan
An analysis of targeted attacks from 2005 to 2007
59 min
Let Them Fail
An Introduction to Massively Distributed Finance or "Cloud…
39 min
DIY Survival
How to survive the apocalypse or a robot uprising
37 min
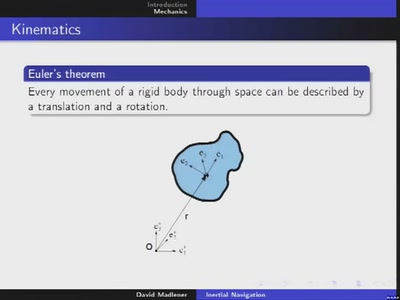
Inertial navigation
Rigid body dynamics and its application to dead reckoning

61 min
Ten years after ‚We Lost The War‘
The future does not look much brighter than ten years ago.…
61 min
Reducing Carbon in the Digital Realm
How to understand the environmental impact of the digital…

30 min
Biometrie ist cool (nicht nur Biometrie)
wer ist Dein Gegner?

37 min
Eliminating the database bottleneck for proper horizontal scalability
Using embeddable databases to allow true and simple…
36 min
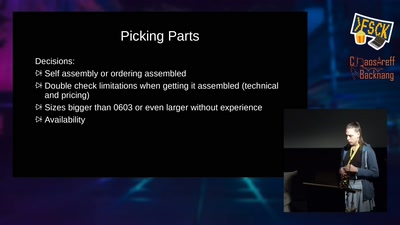
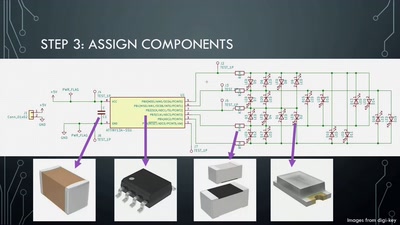
Artistic PCB Design and Fabrication
From doodle to manufacture: how I make mechanically…
53 min
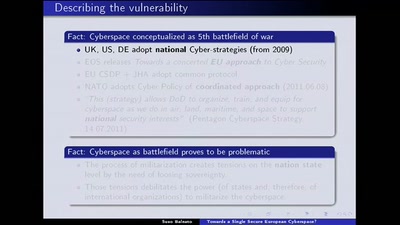
Towards a Single Secure European Cyberspace?
What the European Union wants. What the hackerdom can do..
49 min
Mining Search Queries
How to discover additional knowledge in the AOL query logs

60 min
the possibility of an army
phone verified accounts bringing the Hessian army back to…
61 min
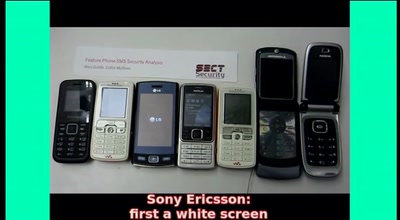
SMS-o-Death
From analyzing to attacking mobile phones on a large scale.
55 min
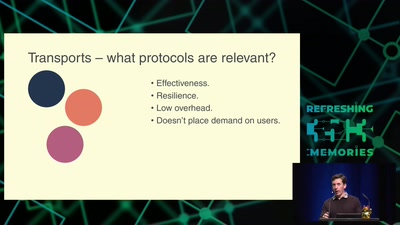
Cat & Mouse: Evading the Censors in 2018
Preserving access to the open Internet with circumvention…
32 min
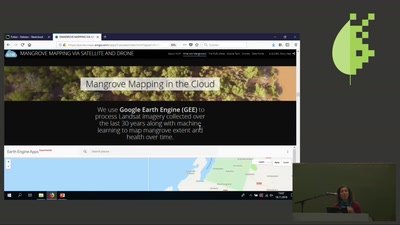
Mangrove Conservation via Satellite
using the latest technology to map and monitor mangroves
27 min
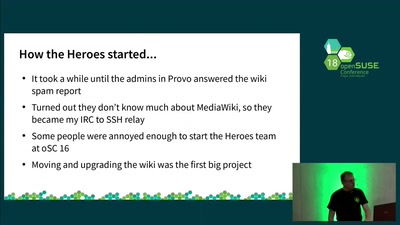
Heroes, not Superheroes
What the Heroes would prefer not to tell you ;-)

57 min
Cybercrime Convention
Hacking on its way to become a criminal act?
57 min
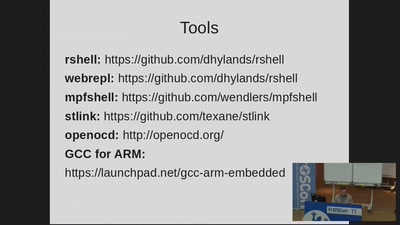
Python für das Internet der Dinge
Einführung in MicroPython für ESP8266 und Cortex-M4…

45 min
USB-Stick zähmen leicht gemacht
Verteidigung gegen BadUSB & Co. für 30 Euro oder weniger
30 min