Search for "Adam Wight" returned 122 results
35 min
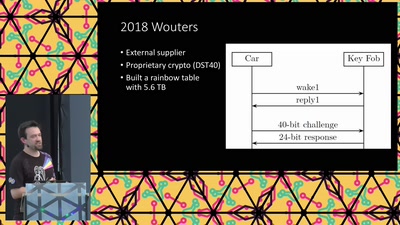
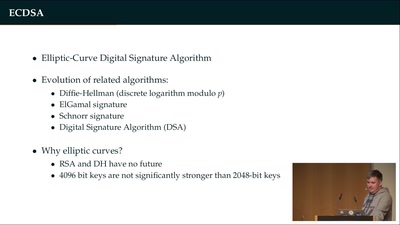
Wallet Security
How (not) to protect private keys
58 min
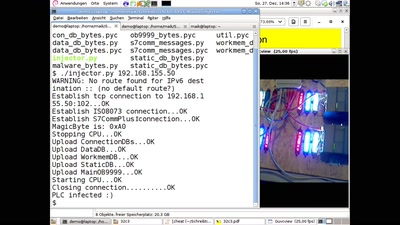
PLC-Blaster
Ein Computerwurm für PLCs
41 min
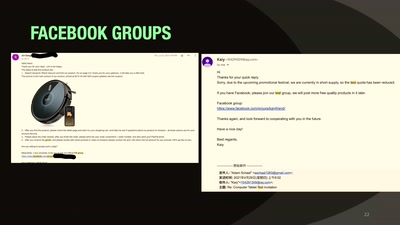
Our Time in a Product Review Cabal
And the malware and backdoors that came with it.
47 min
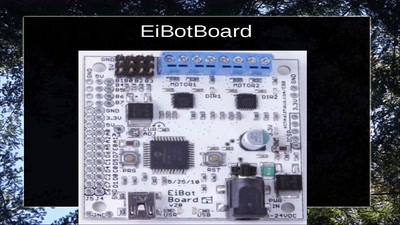
Hillbilly Tracking of Low Earth Orbit
Repurposing an Inmarsat Dish

77 min
Feminist Perspectives
Inclusive and Diverse Spaces and Communities
65 min
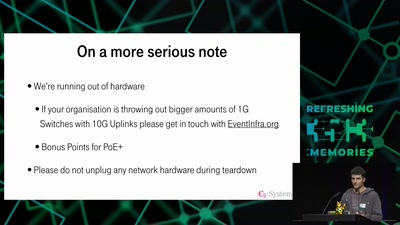
35C3 Infrastructure Review
Up and to the right: All the statistics about this event…

61 min
How Many Planets in Our Solar System? Glad You Asked!
How Astronomy Knew 6 Planets, Then Found 20 More, Then Went…
34 min
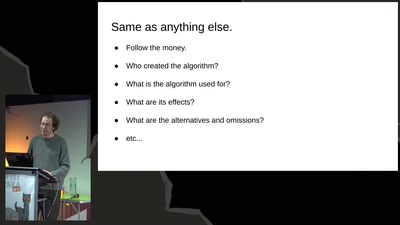
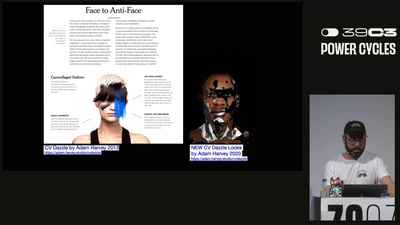
Machine Vision
Vom Algorithmus zum Baumpilz im digitalen Metabolismus
58 min
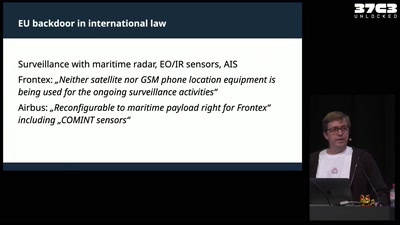
A Libyan Militia and the EU - A Love Story?
Open-Source investigating Tareq Ben Zeyad Brigade and their…
61 min
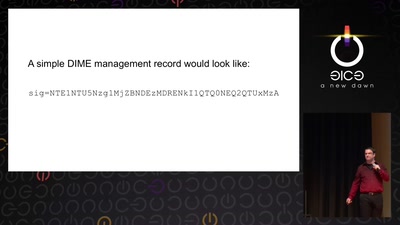
Now I sprinkle thee with crypto dust
Internet reengineering session
33 min