Search for "Ivan March" returned 91 results

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time

31 min
A Tale of Two Leaks:
How Hackers Breached the Great Firewall of China

64 min
Cory Doctorow – Fireside Chat
Reading and Q&A

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
61 min
Email authentication for penetration testers
When SPF is not enough

54 min
What Price the Upload Filter?
The history and costs of government exceptional access
64 min
Source Code and Cross-Domain Authorship Attribution
The Role of Stylometry in Privacy
58 min
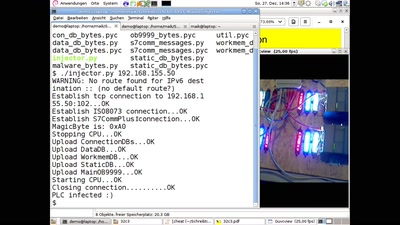
PLC-Blaster
Ein Computerwurm für PLCs

39 min
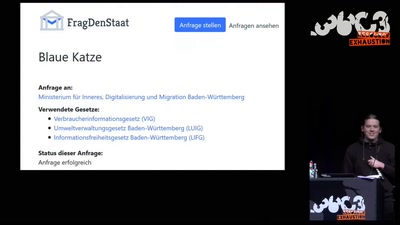
Brennende Wälder und Kommentarspalten
Klimaupdate mit dem FragDenStaat Climate Helpdesk
19 min
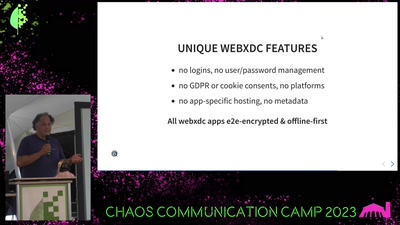
Delta Chat messenger
unlocking the potential of e-mail and the web
63 min