Search for "Jossi" returned 45 results
29 min
Thinking About openSUSE HCL
Let's Keep HCL Updated

55 min
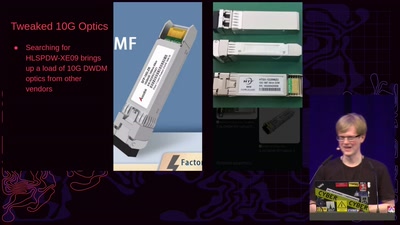
Technological art off the trodden tracks
Artists (mis)using technology

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
29 min
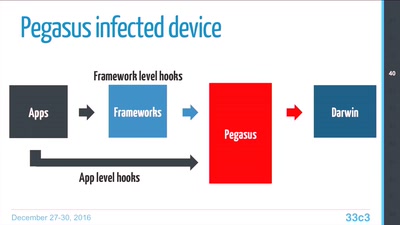
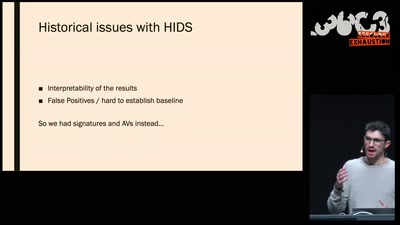
Pegasus internals
Technical Teardown of the Pegasus malware and Trident…
44 min
What the cyberoptimists got wrong - and what to do about it
Tech unexeptionalism and the monopolization of every…
32 min
The Case for Scale in Cyber Security
Security Track Keynote

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database

32 min
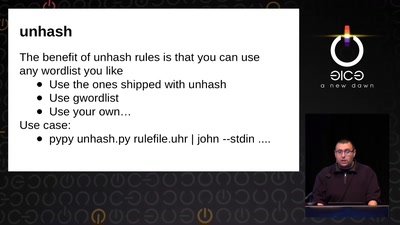
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
63 min
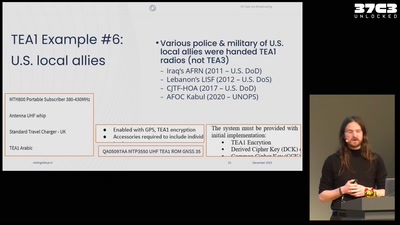
All cops are broadcasting
TETRA unlocked after decades in the shadows
36 min