Search for "Os Keyes" returned 637 results
25 min
Keys of Fury
Type In Beyond the Scrolling Horizon
59 min
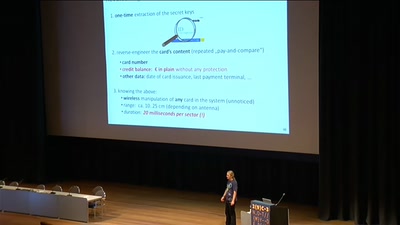
Milking the Digital Cash Cow
Extracting Secret Keys of Contactless Smartcards
64 min
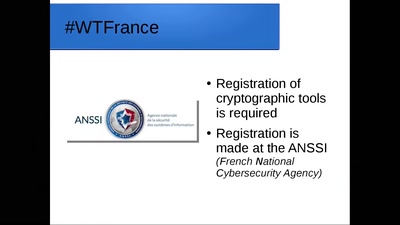
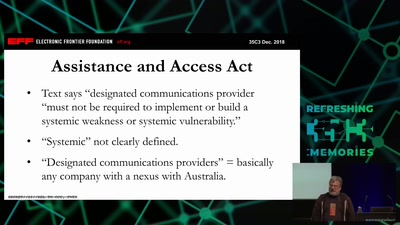
It Always Feels Like the Five Eyes Are Watching You
Five Eyes’ Quest For Security Has Given Us Widespread…
62 min
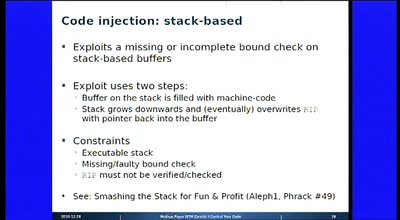
I Control Your Code
Attack Vectors Through the Eyes of Software-based Fault…
35 min
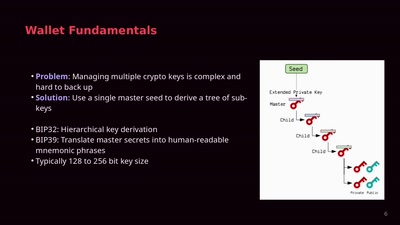
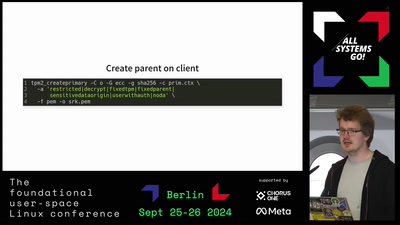
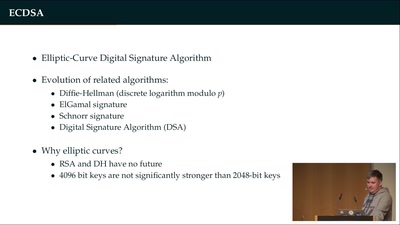
Wallet Security
How (not) to protect private keys
15 min
The new zypper-keys-plugin
The easy way of RPM repo key management
58 min
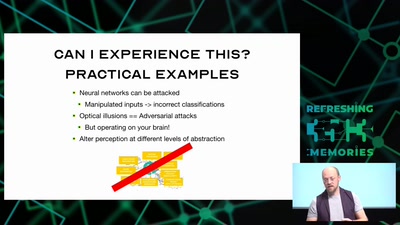
Hacking how we see
A way to fix lazy eye?
45 min
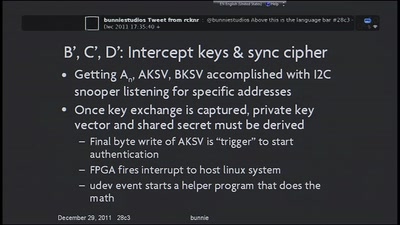
Implementation of MITM Attack on HDCP-Secured Links
A non-copyright circumventing application of the HDCP…
44 min
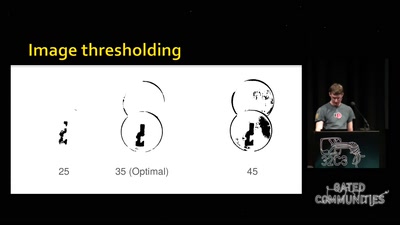
Replication Prohibited
3D printed key attacks

37 min