Events for tag "22c3"
52 min
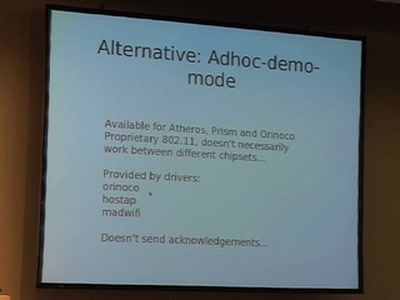
WiFi Long Shots
Wireless connections of 20km and more

49 min
Old Skewl Hacking - InfraRed updated
MMIrDA - Major Malfunction's InfraRed Discovery Application

49 min
Access to Knowledge
Copyright, Patents and Politics at the World Intellectual…
59 min
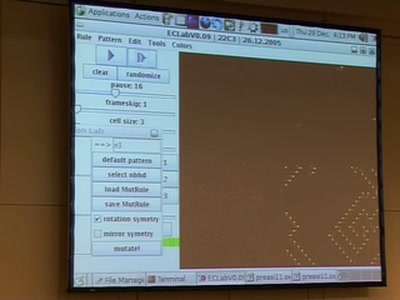
EvoCell - free software for evolving cellular automata
Exploring the huge space of possible cellular automata by…
56 min
Towards the first Free Software GSM Phone
Reverse Engineering the Motorola EZX (A768,A780,E680)…

63 min
Wargames - Hacker Spielen
Männliche Identitätskonstruktion und spielerische…

59 min
Logical Language Lojban
A Hackers' /Spoken/ Language?!

38 min
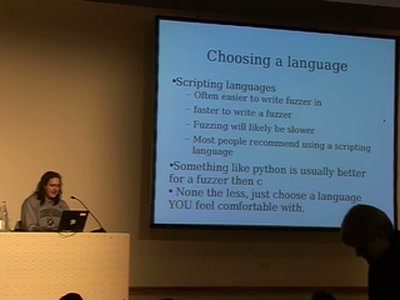
Autodafé: An Act of Software Torture
Presentation of an innovative buffer overflow uncovering…
53 min
WarTracking
Satellite Tracking, harvesting and security

49 min
Syscall proxying fun and applications
Introduction to syscall proxying and applications for in…
46 min
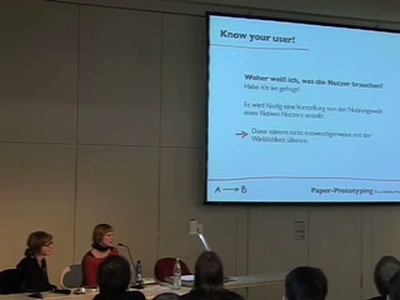
Paper-Prototyping Workshop
Eine Usability-Methode

61 min
The Realtime Podcast
Everything you need to know about Podcasting

52 min
3G Investigations
Scanning your GPRS/UMTS IP network for fun and profit
![Advanced Buffer Overflow Methods [or] Smack the Stack](https://static.media.ccc.de/media/congress/2005/22C3-491-en-advanced_buffer_overflow_methods.jpg)
11 min
Advanced Buffer Overflow Methods [or] Smack the Stack
Cracking the VA-Patch

62 min
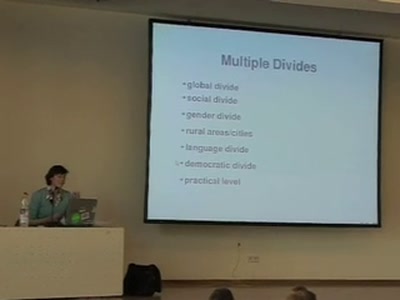
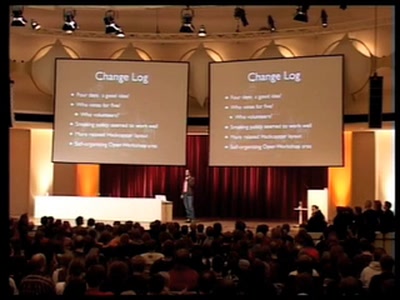
A way to fuzzy democracy
Using modern communication to transform the way we make…

107 min
Hacker Jeopardy
The one and only hacker quizshow

48 min
Rückschau auf die BigBrotherAwards 2005
Datenkraken beim Kragen packen
53 min
Private investigations in searching
How to find any book (and many other roadkills) on the…

57 min
Sicherheit vs. Überwachung
Videoüberwachung am Beispiel des Congressgebäudes
59 min
Writing better code (in Dylan)
Fast development of object-oriented functional programs
113 min
"Xbox" and "Xbox 360" Hacking
17 Mistakes Microsoft Made in the Xbox Security System &…

53 min
Urheberrecht
Fakten, Mythen, Geschichte(n) und mögliche Zukünfte

64 min
Covert Communication in a Dark Network
A major new version of freenet
53 min
GNU/Linux für Blinde und Sehbehinderte
Erfahrungen aus der Praxis

69 min
Entschwörungstheorie
Verschwörungstheoretiker sind hinter mir her!

49 min
Applied Machine Learning
Brief Introduction into Machine Learning followed by…

43 min
Lightning Talks Day 1
Nine five minutes talks by various speakers

47 min
Peer-to-peer under the hood
An in-depth look at p2p algorithmics

50 min
Videoüberwachung an deutschen Hochschulen
oder: "Über meine Maßnahmen gebe ich keine Auskunft"
58 min
Hashing Trusted Computing
Der aktuelle Stand

55 min
Technological art off the trodden tracks
Artists (mis)using technology

53 min
Erste Hilfe für Nerds und Geeks
Wie überlebe ich (ohne nennenswerten Schäden) einen…

54 min
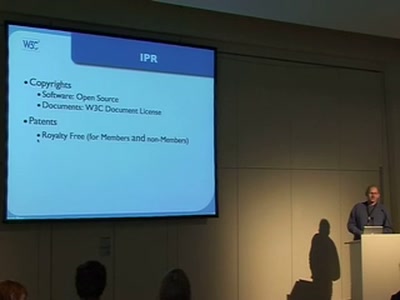
W3C on Mobile, CSS, Multimodal and more
A look at the upcoming standards by W3C
49 min
Lightning Talks Day 4
Nine five minutes talks by various speakers

64 min
Security Nightmares 2006
Oder: worüber wir nächstes Jahr lachen werden

38 min
Fnord Jahresrückblick
Was wirklich geschah
53 min
Blackberry: call to arms, some provided
Teach yourself upper management in 22 days

55 min
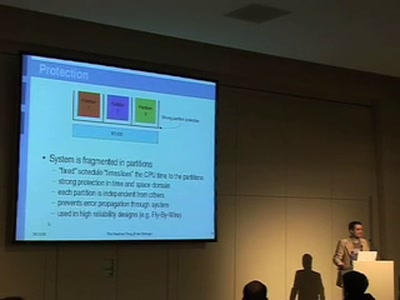
The Future of Virtualization
The "anyOS" paradigm and its implications through…
53 min
The very early Computer Game History
How the games have become the first digital mass product

73 min
We lost the war
Welcome to the world of tomorrow

47 min
Hacking health
Electronic Patient Records in The Netherlands
44 min
The Realtime thing
What the heck is realtime - and what to do with it
42 min
Terminator Genes and GURT - Biological Restrictions Management
Five Years after the announcement of a quasi moratorium
57 min
Secure Code
Why developing Secure Software is like playing Marble…

37 min
Lightning Talks Day 2
Nine five minutes talks by various speakers
58 min
The Right Track
A new approach to copyright in the digital world

52 min
Recent Developments in EU Data Retention proposals
Commission vs. Council - the lesser of two evils?
52 min
Personal experiences bringing technology and new media to disaster areas
Experiences from Iraq and post Katrina New Orleans

53 min
Die BioP-II-Studie des BSI
Biometrische Feldtests in Europa

43 min
Anonymous Data Broadcasting by Misuse of Satellite ISPs
An open-source project to develop a tool for broadband…
51 min
Intrusion Detection Systems
Elevated to the Next Level

56 min
Sony BMGs digitaler Hausfriedensbruch
Über die Durchsetzung industrieller Interessen um jeden…
58 min
Changing Realities
Innovation, user-creation, activism and entrepreneurship in…
60 min
The grey commons
Strategic considerations in the copyfight.

47 min
Software Patenting
Adequate means of protection for software.
64 min
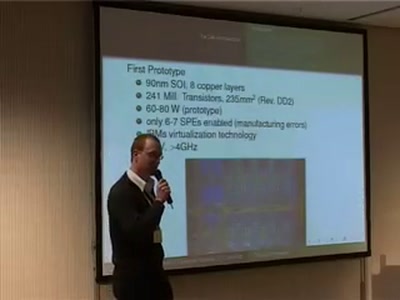
The Cell Processor
Computing of Tomorrow or Yesterday
56 min
Anonymität im Internet
Rechtliche und technische Aspekte

167 min
Elektronische Gesundheitskarte und Gesundheitstelematik - 1984 reloaded?
Eine unendliche Geschichte - Kapitel: Die Sümpfe der…
54 min
Free Software and Anarchism
does this compute?

53 min
The truth about Nanotechnology
A concise introduction to what NT is, what it can't do yet…

65 min
Was ist technisches Wissen?
Philosophische Grundlagen technischer Wissenschaften

64 min
A guided tour to European IT lobbying
An investigation into intransparency

46 min
Honeymonkeys
Chasing hackers with a bunch of monkeys
67 min
Geometrie ohne Punkte, Geraden & Ebenen
Buckminster Fullers Theorie und Praxis einer Wissenschaft…

60 min
Exploring Protocols and Services on Internet Connected Embedded Devices
Looking for Insecurities
56 min
Hacking CCTV
Watching the watchers, having fun with cctv cameras, making…
58 min
Open Source, EU funding and Agile Methods
Sprint methodology in funded OSS projects

49 min
Hexenbesen und heiliger Gral
Vorläufige und subjektive Gedanken zur inhaltlichen…

57 min
Cybercrime Convention
Hacking on its way to become a criminal act?

66 min
COMPLETE Hard Disk Encryption with FreeBSD
Learn how to effectively protect not only your data but…
59 min
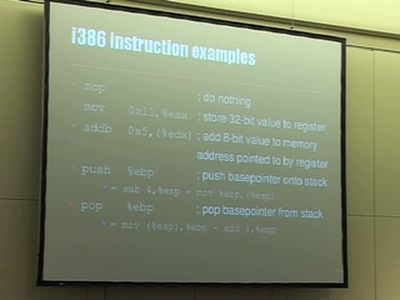
Understanding buffer overflow exploitation
The fascinating interplay of CPU, stack, C-compiler and…
45 min
Hopalong Casualty
On automated video analysis of human behaviour
59 min
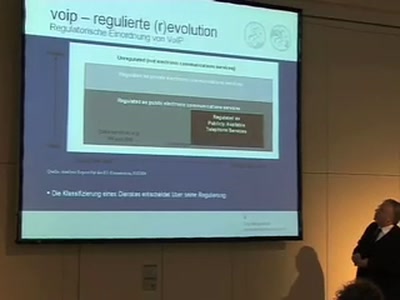
VoIP 2005 - Regulierte Revolution
Ansätze für die Regulierung von VoIP und NGN im vergangenen…

56 min
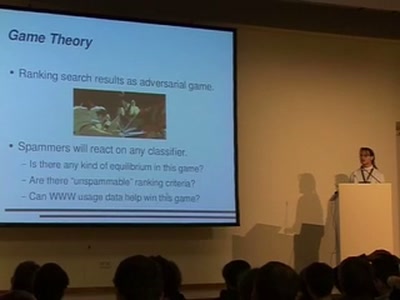
Search Engines - Oracles of the Information Society
The Saga continues: Search Engines, Technology, Politics,…

49 min
Hacking Data Retention
How bureaucrats fail to fight terror
53 min
Privaterra - Report from the field
IT Security and Human Rights organizations - The needs, the…
38 min
Quantum Entanglement
An introduction

35 min
Learning cryptography through handcyphers
Shaping a digital future with ancient wisdom

43 min
CCC Jahresrückblick
Ein Überblick über die Aktivitäten des Clubs 2005

59 min
Literarisches Code-Quartett
The good, the bad, and the ugly

45 min
Finding and Preventing Buffer Overflows
An overview of static and dynamic approaches
46 min
Atmel AVR für Dummies
Was ist denn nun eigentlich so ein 'Interrupt'?

49 min
VoIPhreaking
Introduction to SIP Hacking

59 min
e-Voting: The silent decline of public control
Why German voting machines do not meet the requirements of…
56 min
Corp vs. Corp
Profiling Modern Espionage

93 min
Bluetooth Hacking - The State of The Art
A roundup and live demonstrations of all currently known…

52 min
Hacking into TomTom Go
Reverse-Engineering des Embedded-Linux-Navigationssystems

58 min
22C3: Private Investigations
Opening Show and Keynote Speech

60 min
On working memory and mental imagery
How does the brain learn to think?

61 min
PyPy - the new Python implementation on the block
Language/VM R&D, whole program type inference, translation…
51 min
I See Airplanes!
How to build your own radar system

65 min
Lightning Talks Day 3
Nine five minutes talks by various speakers

52 min
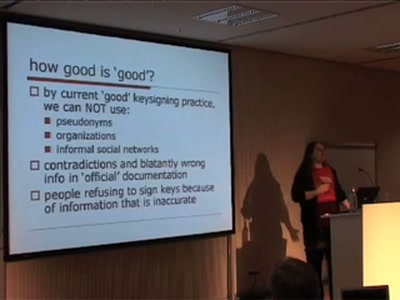
Digital Identity and the Ghost in the Machine
"Once I Was Lost But Now I've Been Found"

60 min
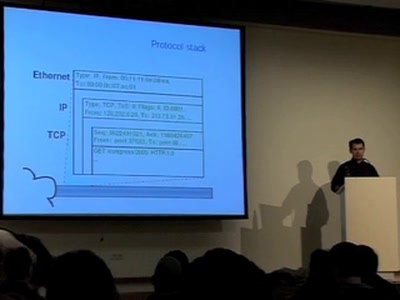
Black Ops Of TCP/IP 2005.5
New Explorations: Large Graphs, Larger Threats
54 min
Collateral Damage
Consequences of Spam and Virus Filtering for the E-Mail…

54 min
Internet Voting in Estonia
First-ever pan-national official occasion.
47 min
RFID - overview of protocols, librfid implementation and passive sniffing
ISO14443, ISO15693, their GPL librfid implementation and…

59 min
Vulnerability markets
What is the economic value of a zero-day exploit?

46 min
Have you hugged your Mac today?
Ein audiovisuelles Live-Feature
49 min
Lawful Interception in VoIP networks
Old Laws and New Technology the German Way
55 min
The Web according to W3C
How to turn your idea into a standard
54 min
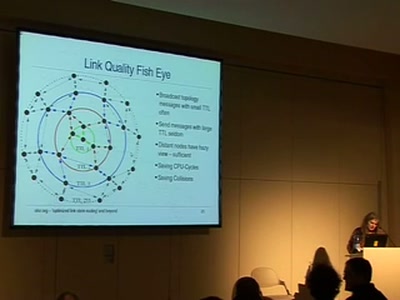
Community mesh networking
Ubiquitous wireless mesh clouds with olsrd from olsr.org

27 min
Message generation at the info layer
Basic introduction in coding on unvirtual realities.
44 min
22C3 Closing Event
Famous last words

52 min
Military intelligence for terrorists(tm)
A lamer's introduction to retrieving "sensitive"…

44 min
Esperanto, die internationale Sprache
Eine gut strukturierte Sprache für Geeks und die EU

56 min
WSIS - The Review
Hacking a Dictatorship

45 min
Hosting a Hacking Challenge - CTF-style
Background information on CIPHER, an international…
42 min