Search for person "Lucia und Ben" returned 89 results
38 min
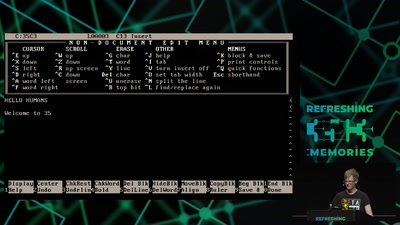
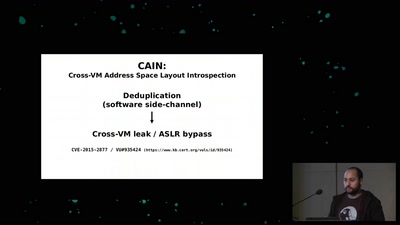
A deep dive into the world of DOS viruses
Explaining in detail just how those little COM files…
35 min
Access to Tools (in Graphic design)
Werkzeuge für Typografie, Grafikdesign und einen…
59 min