Search for person "Walter van Holst" returned 143 results
87 min
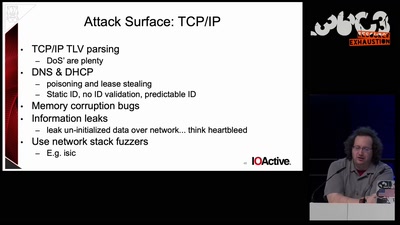
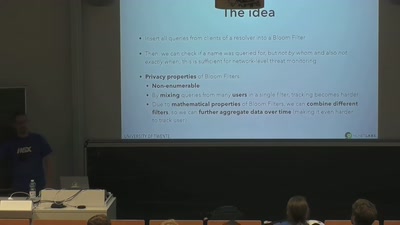
DNS privacy and security
Chaos Colloquium #1

23 min
E-ID? Nicht ohne Privacy by Design!
Die DSGVO in der Praxis
49 min
Cyborg Teams
Happy humans, tired machines
40 min
Court in the Akten
OpenSchufa und OffeneGesetze

63 min
LightKultur in Deutschland
Clubkultur oder wie modern ist unser Kulturbegriff?

61 min
Avoiding kernel panic: Europe’s biggest fails in digital policy-making
How the institutions fuck up, and how we fuck it up as well

25 min