Search for "@FiLiS" returned 648 results
58 min
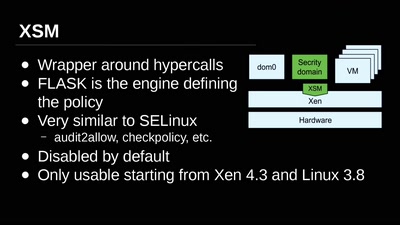
Virtual Machine Introspection
From the Outside Looking In
34 min
Little Services, Big Risks
Extending capability-based security models to achieve…
36 min
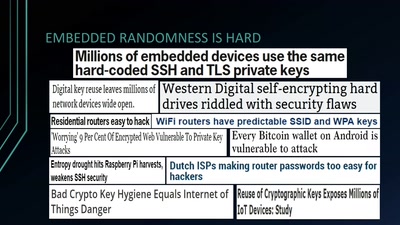
Wheel of Fortune
Analyzing Embedded OS Random Number Generators

60 min
What does Big Brother see, while he is watching?
Uncovering images from the secret Stasi archives.
10 min
Premiere: We love surveillance
#7reasons
60 min
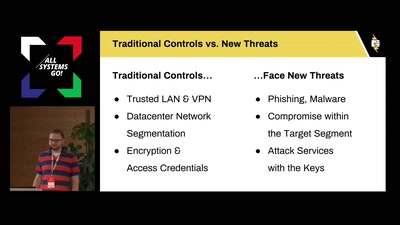
Sneaking In Network Security
Enforcing strong network segmentation, without anyone…
58 min
07KINGSTON25 JAMAICA: MALARIA UPDATE Dispatches from Fort Meade
Reporting on the secret trial of Chelsea Manning
37 min
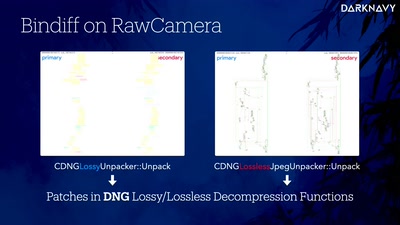
Inside the AMD Microcode ROM
(Ab)Using AMD Microcode for fun and security
55 min
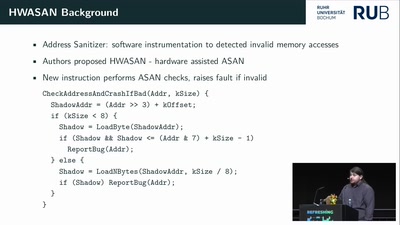
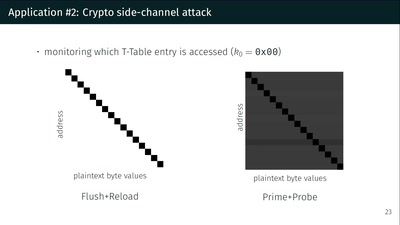
What could possibly go wrong with <insert x86 instruction here>?
Side effects include side-channel attacks and bypassing…
60 min
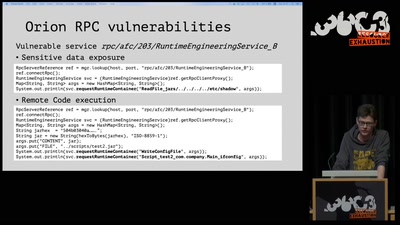
On the insecure nature of turbine control systems in power generation
A security study of turbine control systems in power…
39 min
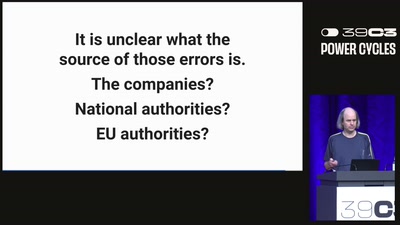
Greenhouse Gas Emission Data
Public, difficult to access, and not always correct
60 min
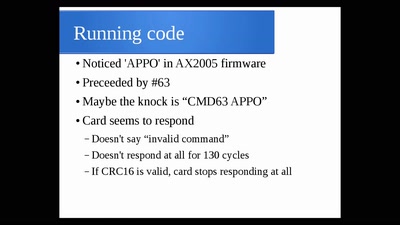
The Exploration and Exploitation of an SD Memory Card
by xobs & bunnie
52 min