Search for "Eric" returned 284 results

60 min
Quantum Cryptography
from key distribution to position-based cryptography
58 min
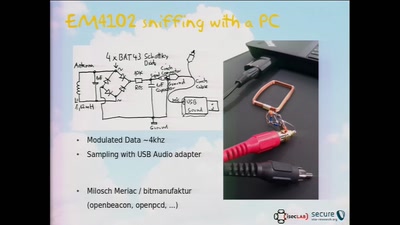
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems
33 min
Turing Complete User
What can be done to protect the term, the notion and the…
60 min
Lifting the Fog on Red Star OS
A deep dive into the surveillance features of North Korea's…

62 min
Corporate surveillance, digital tracking, big data & privacy
How thousands of companies are profiling, categorizing,…
58 min
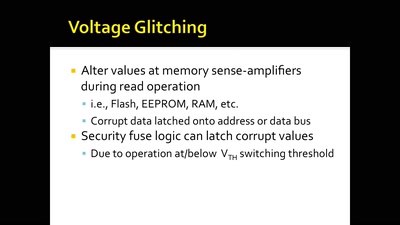
Glitching For n00bs
A Journey to Coax Out Chips' Inner Secrets
42 min
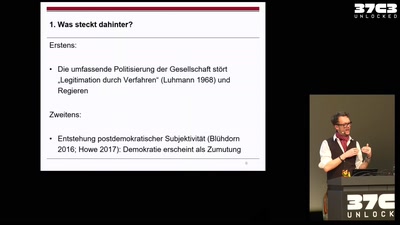
Ist die Demokratie noch zu retten?
Politikwissenschaftliche Demokratieforschung in der Krise

39 min
Gamified Control?
China's Social Credit Systems

60 min
Österreich: Der Kampf gegen unkontrollierte Massenüberwachung
Geheimdienste kontrolliert man am besten, indem man ihre…
32 min
Visceral Systems
Approaches to working with sound and network data…
60 min
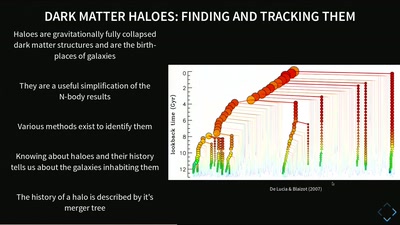
Simulating Universes
What Virtual Universes Can Tell Us About Our Own
64 min
"Exploit" in theater
post-existentialism is the question, not post-privacy
60 min
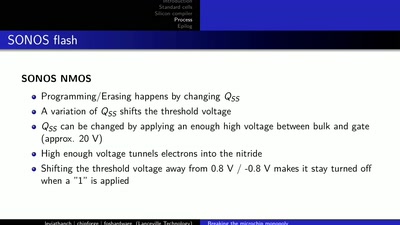
LibreSilicon
Decentralizing semiconductor manufacturing

37 min
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
44 min
What the cyberoptimists got wrong - and what to do about it
Tech unexeptionalism and the monopolization of every…
62 min
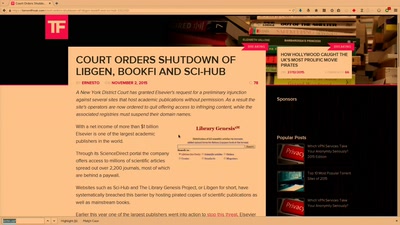
Public Library/Memory of the World
Access to knowledge for every member of society
60 min