Search for "Dave" returned 3492 results
62 min
Public Library/Memory of the World
Access to knowledge for every member of society

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
53 min
Console Hacking 2016
PS4: PC Master Race

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
62 min
Getting software right with properties, generated tests, and proofs
Evolve your hack into robust software!
58 min
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
47 min
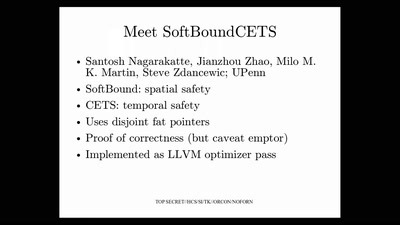
Bug class genocide
Applying science to eliminate 100% of buffer overflows
44 min
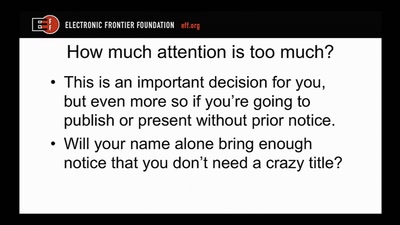
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers
29 min
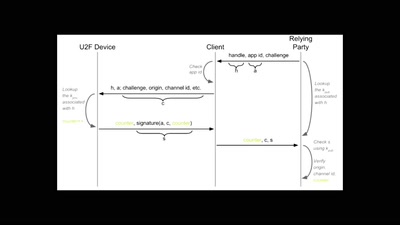
What de.fac2?
Attacking an opensource U2F device in 30 minutes or less
60 min
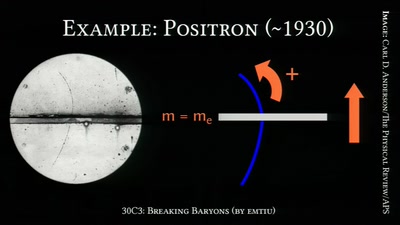
Breaking Baryons
On the Awesomeness of Particle Accelerators and Colliders
58 min
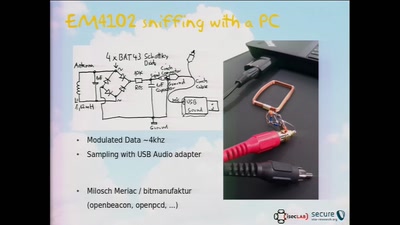
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems
43 min