Search for "c-atre" returned 3715 results
55 min
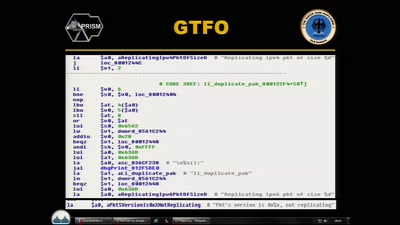
Cyber Necromancy
Reverse Engineering Dead Protocols
38 min
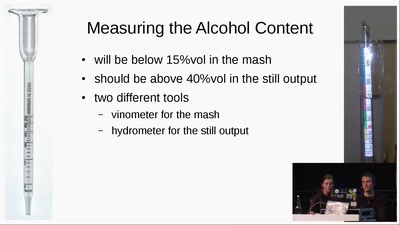
Schnaps Hacking
from apple to schnaps -- a complete diy-toolchain
27 min
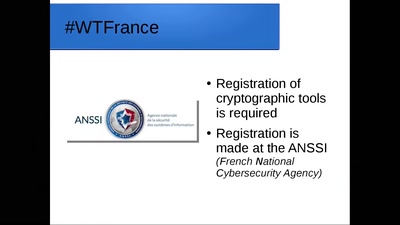
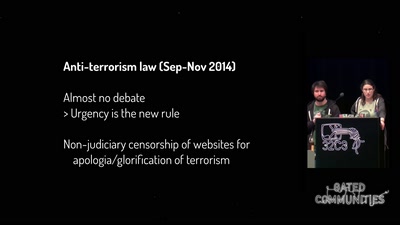
One year of securitarian drift in France
From the Bill on Intelligence to the State of Emergency
33 min
The Transhumanist Paradox
Deciding between technological utopias in a liberal state
61 min
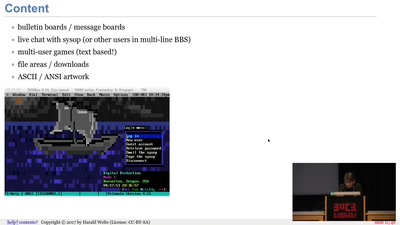
BBSs and early Internet access in the 1990ies
Modems, FIDO, Z-Netz, Usenet, UUCP, SLIP and ISDN
57 min
A New Dark Age
Turbulence, Big Data, AI, Fake News, and Peak Knowledge
46 min
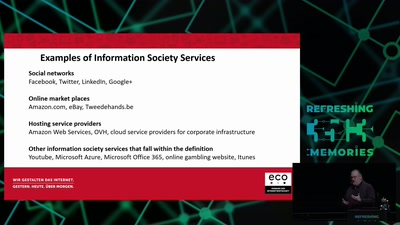
Electronic Evicence in Criminal Matters
An introduction and critique of the EC proposal for a…
39 min
DISNOVATION.ORG
Disobedient Innovation
33 min
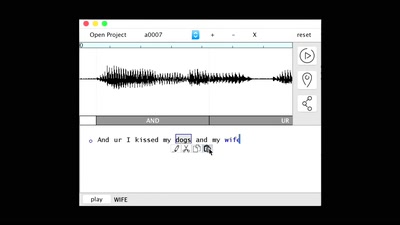
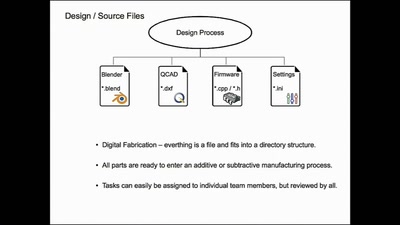
Structuring open hardware projects
experiences from the “i3 Berlin” 3D printer project with…
46 min
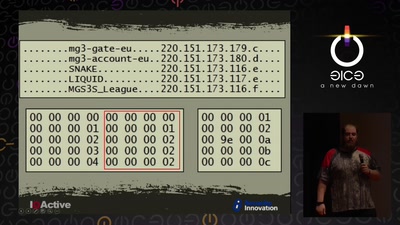
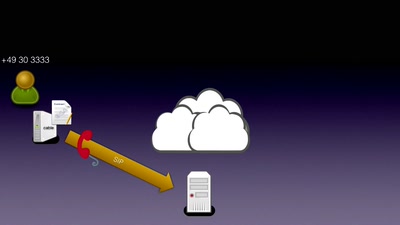
CounterStrike
Lawful Interception

60 min
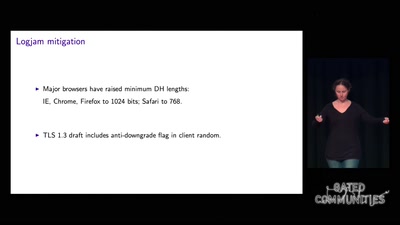
Quantum Cryptography
from key distribution to position-based cryptography

54 min
What Price the Upload Filter?
The history and costs of government exceptional access
29 min
The Pirate Cinema
Creating mash-up movies by hidden activity and geography of…
60 min
Beyond your cable modem
How not to do DOCSIS networks
31 min
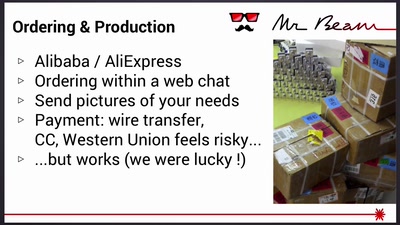
Mr Beam goes Kickstarter
Lessons learned from crowdfunding a hardware project
61 min
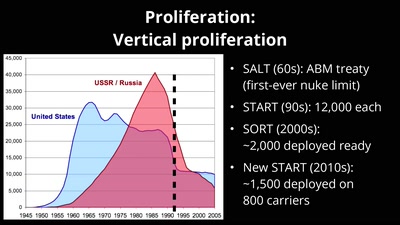
What Ever Happened to Nuclear Weapons?
Politics and Physics of a Problem That's Not Going Away

41 min