Search for "kay" returned 3885 results

30 min
Mobile devices and openSUSE, is it posible?
It is time to check if we can use a mobile device with a…
60 min
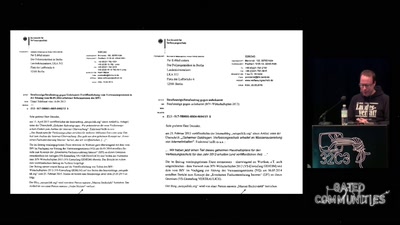
Ein Abgrund von Landesverrat
Wie es dazu kam und was daraus zu lernen ist

17 min
kanku - Bridging the gap between OBS and developers
A convenient way to work with your OBS built images
32 min
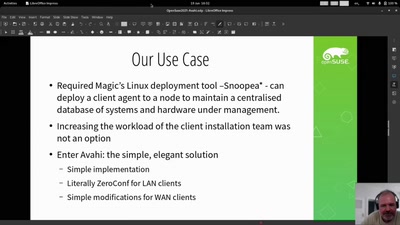
Live: Avahi / Zeroconf: Some magic sauce that's about more than files and printers
Hand editing config files for local deployment? Say hi to…

60 min
The Grand EU Data Protection Reform
A latest battle report by some key actors from Brussels
52 min
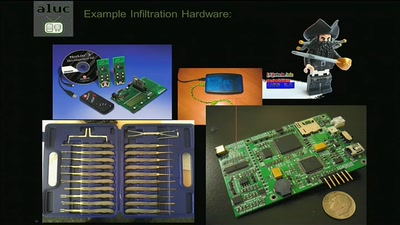
The engineering part of social engineering
Why just lying your way in won't get you anywhere
37 min
Self-documenting computation
What is the best way to present programs to non-programmers?

58 min
Cray-1, Ikone des Supercomputing
Wie die Maschine zur Welt kam, und was danach passierte

59 min
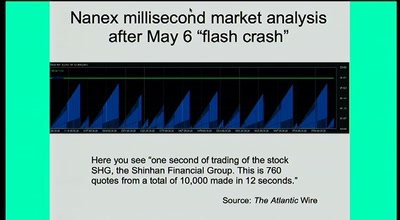
Vulnerability markets
What is the economic value of a zero-day exploit?
61 min
Human body as an electric IO system
Hacking your brain, and other body parts. Debunking myths…
31 min
Growing Up Software Development
From Hacker Culture to the Software of the Future
![NSFW: Di[CENSORED]s for privacy](https://static.media.ccc.de/media/events/SHA2017/49-hd.jpg)
28 min
NSFW: Di[CENSORED]s for privacy
Why not give hackers and agencies something to look at . .
60 min