Search for "kay" returned 3885 results

31 min
The DRM Of Pacman
Copy protection schemes of way back then and how they…
59 min
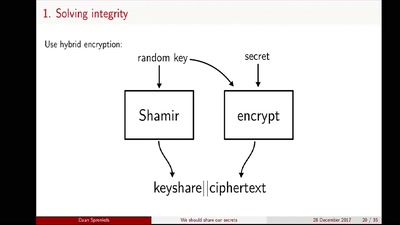
We should share our secrets
Shamir secret sharing: How it works and how to implement it
29 min
SHA2017 Closing
Five days of hacking, this is what happened. You wouldn't…
54 min
Hacking Cisco Phones
Just because you are paranoid doesn't mean your phone isn't…
59 min
Micro Services
Vertical thinking for a simple architecture!
55 min
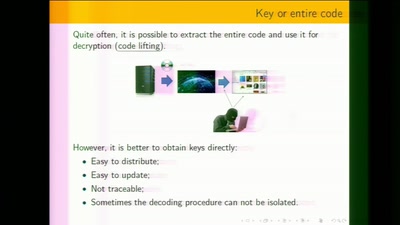
White-Box Cryptography
Survey
55 min
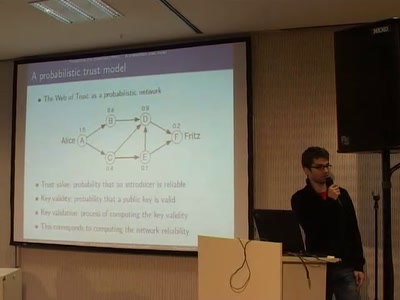
A Probabilistic Trust Model for GnuPG
A new way of evaluating a PGP web of trust by using a…
26 min
Learning from embedded: less is more
...or how to use any existing SUSE OS variant to meet all…
49 min