Search for "feh" returned 1866 results
57 min
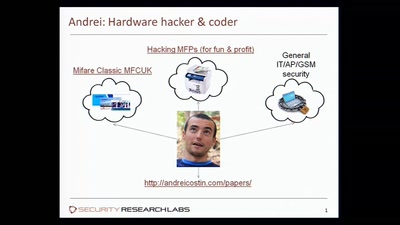
Hacking MFPs
Part2 - PostScript: Um, you've been hacked
40 min
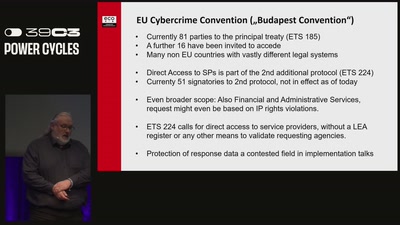
Live, Die, Repeat
The fight against data retention and boundless access to…
42 min
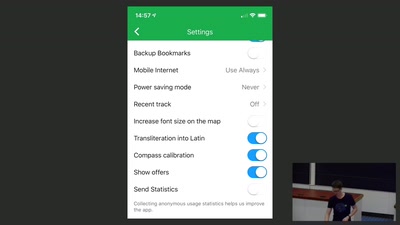
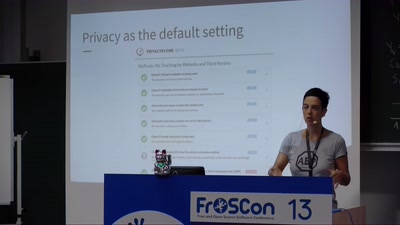
We do Privacy by Design
Best practices and real-life examples
42 min
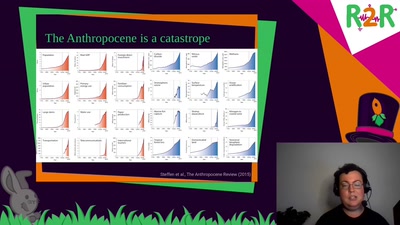
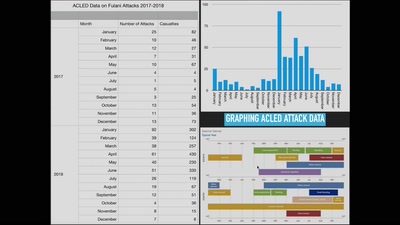
Mapping Doomsday
Using OSINT to monitor and predict environmental conflicts
41 min
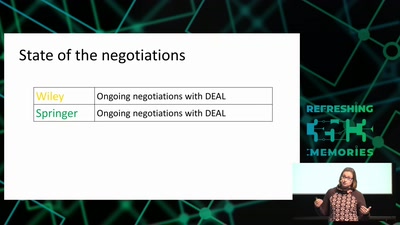
Locked up science
Tearing down paywalls in scholarly communication
31 min
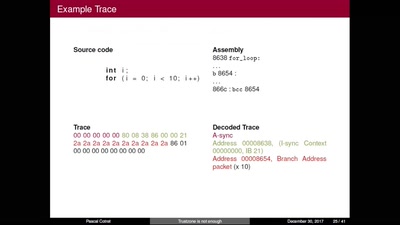
TrustZone is not enough
Hijacking debug components for embedded security

61 min
wallet.fail
Hacking the most popular cryptocurrency hardware wallets
47 min