Search for "Jim" returned 5093 results

60 min
My Robot Will Crush You With Its Soft Delicate Hands!
How to design and fabricate soft robots using everyday…
29 min
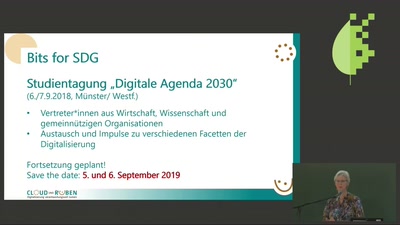
Bits for SDG
Eine Digitale Agenda 2030 für die SDG!
42 min
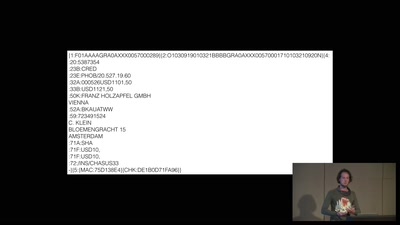
A world without blockchain
How (inter)national money transfers works
32 min
Visceral Systems
Approaches to working with sound and network data…
30 min
All Our Shared Spectrum Are Belong to Us
Visualizing WLAN Channel Usage on OpenWRT
56 min
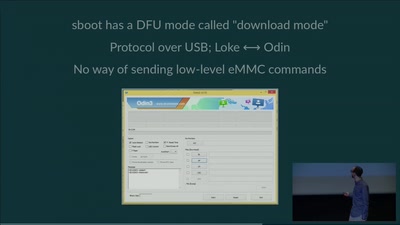
eMMC hacking, or: how I fixed long-dead Galaxy S3 phones
A journey on how to fix broken proprietary hardware by…
30 min
Privacy and Consumer Markets
Reversing the Surveillance Business Model
55 min
The good, the strange and the ugly in 2018 art &tech
On art, AI, hormones hacking and other prospects of a…
32 min
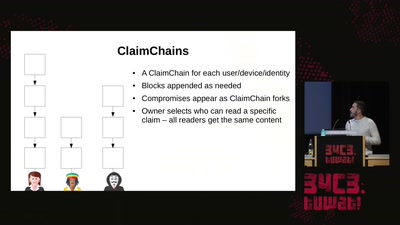
Modern key distribution with ClaimChain
A decentralized Public Key Infrastructure that supports…

32 min
Verified Firewall Ruleset Verification
Math, Functional Programming, Theorem Proving, and an…
51 min
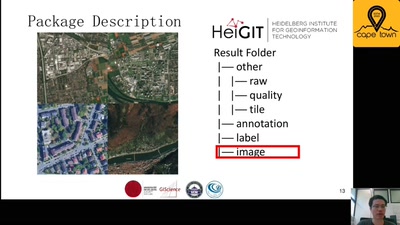
Open Source in the WSN Research
Experiences made with free and open source software in…
30 min
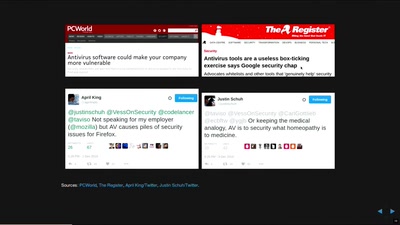
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
30 min
Information Control and Strategic Violence
How governments use censorship and surveillance as part of…

30 min
apertus° AXIOM
The first Open Source Cinema Camera
30 min