Search for "Christian Heck" returned 65 results
43 min
Van Gogh TV - Piazza virtuale
Hallo hallo ist da jemand?
60 min
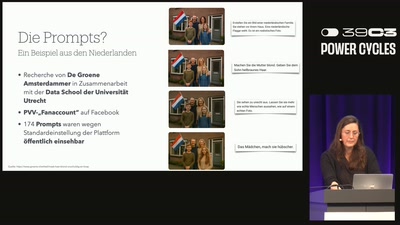
Doomsday-Porn, Schäferhunde und die „niedliche Abschiebung“ von nebenan
Wie autoritäre Akteure KI-generierte Inhalte für Social…

60 min
Quantum Cryptography
from key distribution to position-based cryptography
39 min
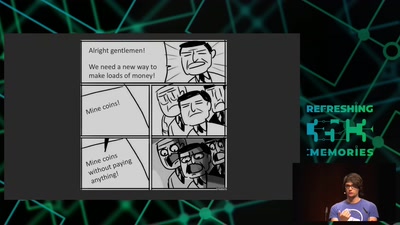
Web-based Cryptojacking in the Wild
When your browser is mining coins for other people
51 min
Uncovering vulnerabilities in Hoermann BiSecur
An AES encrypted radio system
45 min
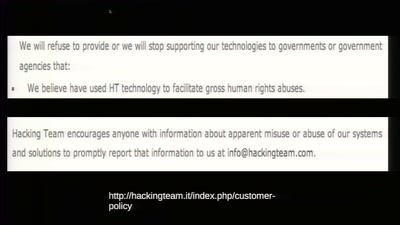
To Protect And Infect
The militarization of the Internet
63 min
Human Rights at a Global Crossroads
Whistleblowers and the Cases of The Snowden Refugees and…
53 min
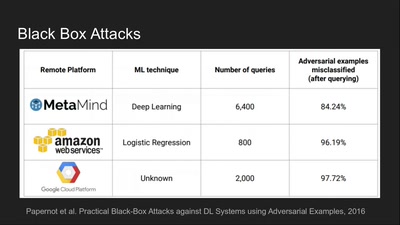
Deep Learning Blindspots
Tools for Fooling the "Black Box"

45 min
Tech(no)fixes beware!
Spotting (digital) tech fictions as replacement for social…

46 min
Maker Spaces in Favelas - Lecture
Engaging social innovation and social innovators

69 min
Telescope Making
How to make your own telescope

135 min
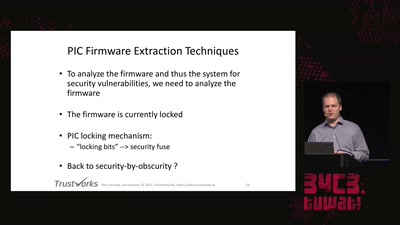
Jahresrückblick des CCC 2018
Refreshing Memories

59 min
Hardsploit: A Metasploit-like tool for hardware hacking
A complete toolbox for IoT security
57 min