Search for "Twi"
prev
next

78 min
Wer hat den Osterhasen vercybert?
91 min
From Unanimity to Anonymity

42 min
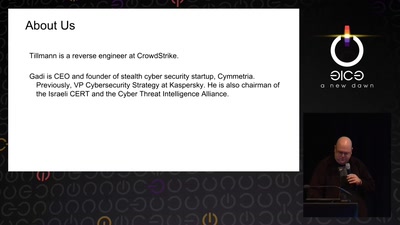
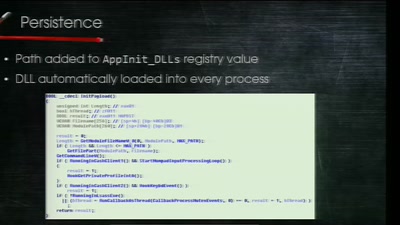
A couple of stories about kernel exploiting
56 min
Stealing Money from ATMs with Malware
61 min
A Deep Technical Analysis
63 min
exploring two decades of transport layer insecurity

52 min
Commission vs. Council - the lesser of two evils?
32 min
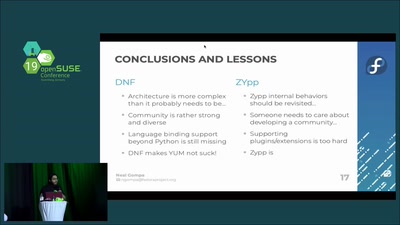
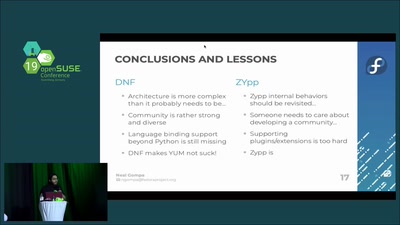
A comparison of the two major RPM package managers
52 min
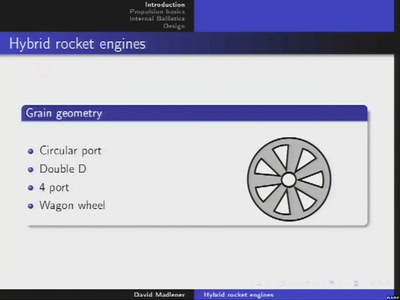
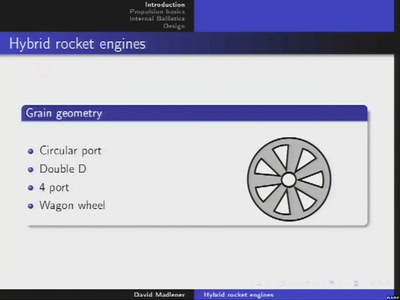
Design and implementation of rocket engines with two-phase…

60 min
Taking stock after two years of net neutrality in the…
48 min
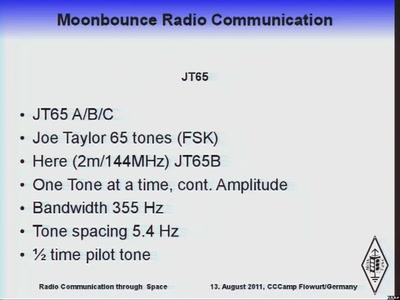
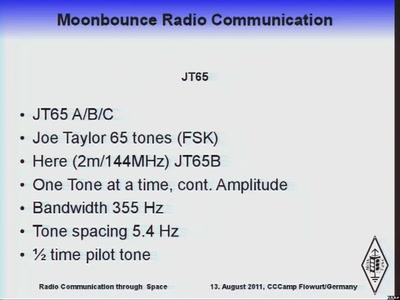
To the Moon and back in two seconds. The joy of light speed…

29 min
WLANs mit Wi-Fi Protected Access (WPA) betreiben
prev
next