Search for "olel" returned 86 results

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
62 min
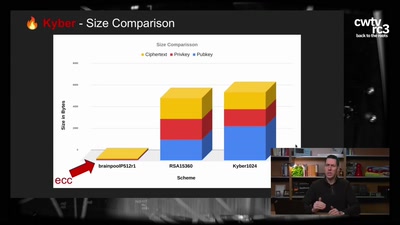
Kyber and Post-Quantum Crypto
How does it work?
32 min
The Case for Scale in Cyber Security
Security Track Keynote
44 min
What the cyberoptimists got wrong - and what to do about it
Tech unexeptionalism and the monopolization of every…

37 min
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…

61 min
Deploying TLS 1.3: the great, the good and the bad
Improving the encrypted the web, one round-trip at a time
60 min
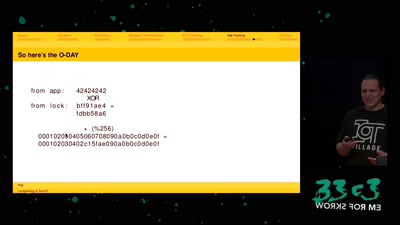
Lockpicking in the IoT
...or why adding BTLE to a device sometimes isn't smart at…
36 min
A Blockchain Picture Book
Blockchain origins and related buzzwords, described in…
61 min
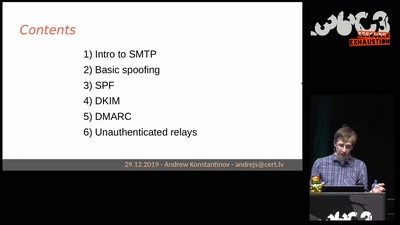
Email authentication for penetration testers
When SPF is not enough
58 min
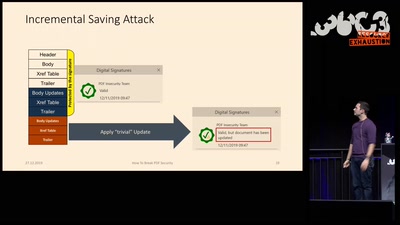
How to Break PDFs
Breaking PDF Encryption and PDF Signatures
53 min
Cryptography demystified
An introduction without maths

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
44 min
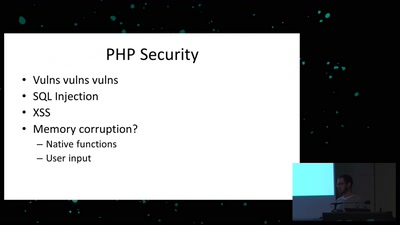
Exploiting PHP7 unserialize
teaching a new dog old tricks
63 min