Search for "LAC team" returned 769 results
58 min
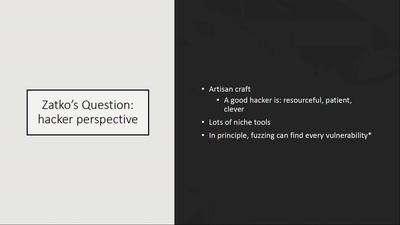
How risky is the software you use?
CITL: Quantitative, Comparable Software Risk Reporting
30 min
Privacy and Consumer Markets
Reversing the Surveillance Business Model

61 min
Copywrongs 2.0
We must prevent EU copyright reform from breaking the…
41 min
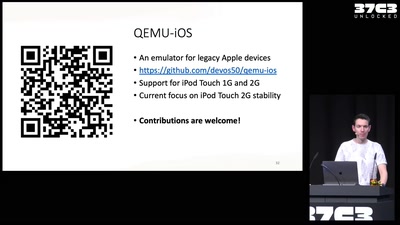
Breathing Life into Legacy: An Open-Source Emulator of Legacy Apple Devices
A Dive into Reverse Engineering and Understanding the iPod…
55 min
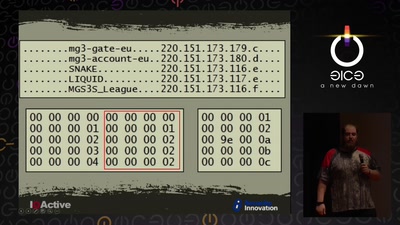
Cyber Necromancy
Reverse Engineering Dead Protocols

66 min
The Snowden Refugees under Surveillance in Hong Kong
A Rapidly Emerging Police State and Imminent Deportation to…
38 min
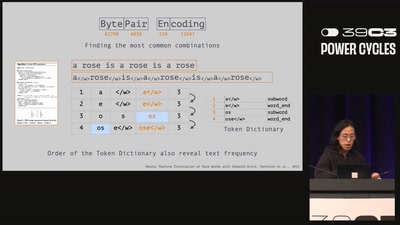
51 Ways to Spell the Image Giraffe:
The Hidden Politics of Token Languages in Generative AI
44 min
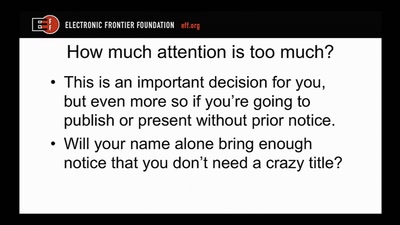
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers

30 min
apertus° AXIOM
The first Open Source Cinema Camera
60 min
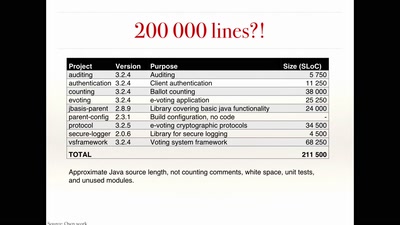
The rise and fall of Internet voting in Norway
Evaluating a complex cryptographic implementation
61 min
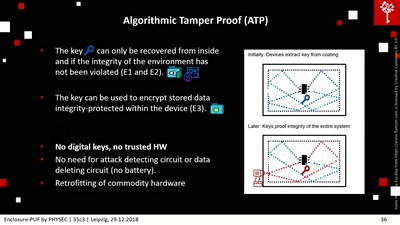
Enclosure-PUF
Tamper Proofing Commodity Hardware and other Applications
101 min
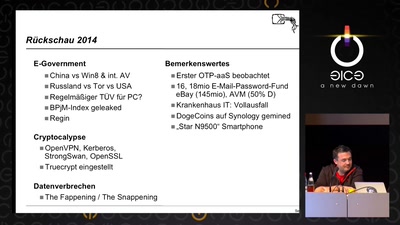
Security Nightmares
Damit Sie auch morgen schlecht von Ihrem Computer träumen.
41 min
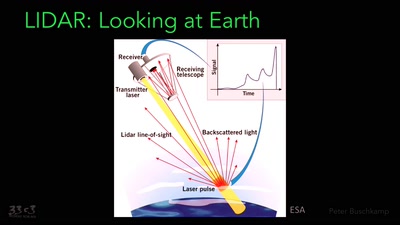
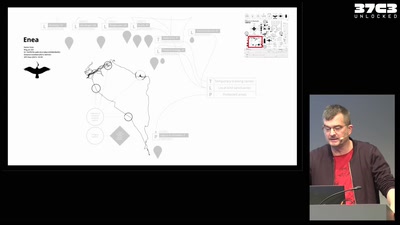
Infrastructure of a migratory bird
Technology and autonomy in more-than-human networks
66 min
31C3 Keynote
A New Dawn
30 min