Search for "Ben H" returned 5946 results
60 min
Why is GPG "damn near unusable"?
An overview of usable security research

60 min
the possibility of an army
phone verified accounts bringing the Hessian army back to…
60 min
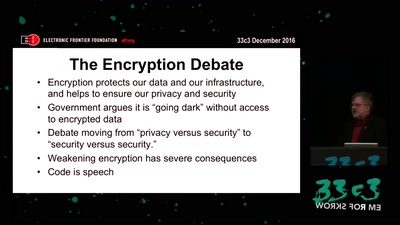
The Fight for Encryption in 2016
Crypto fight in the Wake of Apple v. FBI
39 min
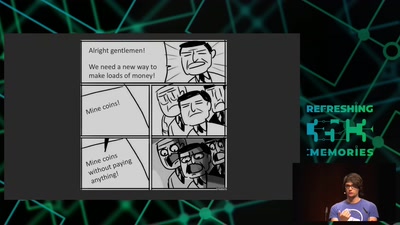
Web-based Cryptojacking in the Wild
When your browser is mining coins for other people
59 min
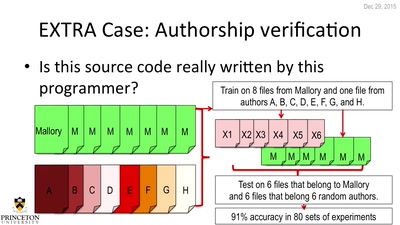
De-anonymizing Programmers
Large Scale Authorship Attribution from Executable Binaries…
54 min
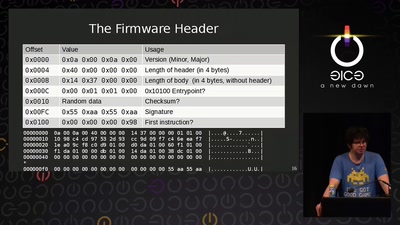
AMD x86 SMU firmware analysis
Do you care about Matroshka processors?

60 min
Hacking Reality
Mixed Reality and multi-sensory communication
30 min
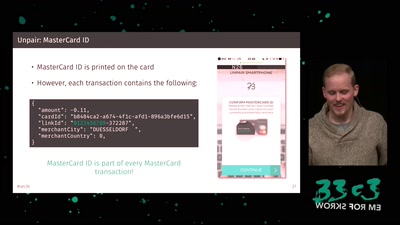
Shut Up and Take My Money!
The Red Pill of N26 Security
28 min
Welcome to the Anthropocene?
(Did) We Accidentally a New Geological Epoch(?)
60 min
The Perl Jam 2
The Camel Strikes Back

32 min
Craft, leisure, and end-user innovation
How hacking is conceived in social science research
61 min
Rocket Kitten: Advanced Off-the-Shelf Targeted Attacks Against Nation States
A Deep Technical Analysis
61 min
Programming FPGAs with PSHDL
Let's create the Arduino for FPGAs
48 min