Search for "Tim" returned 6509 results
120 min
Hacken, dass...?
Ack, die Wette gilt!
40 min
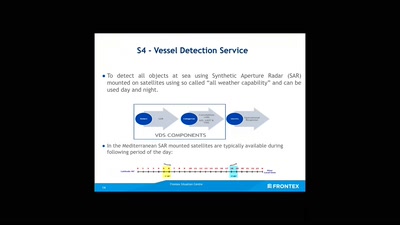
No roborders, no nation, or: smile for a European surveillance propagation
How an agency implements Fortress Europe by degrading…
46 min
You can -j REJECT but you can not hide: Global scanning of the IPv6 Internet
Finding interesting targets in 128bit of entropy
59 min
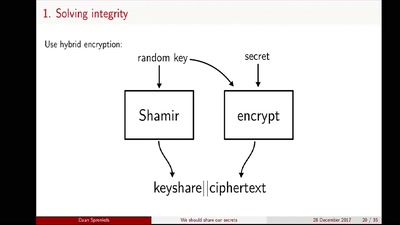
We should share our secrets
Shamir secret sharing: How it works and how to implement it
58 min
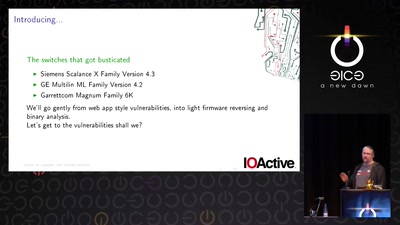
Switches Get Stitches
Industrial System Ownership
62 min
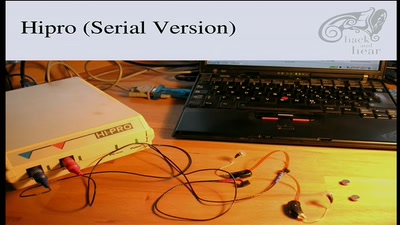
Bionic Ears
Introduction into State-of-the-Art Hearing Aid Technology
30 min
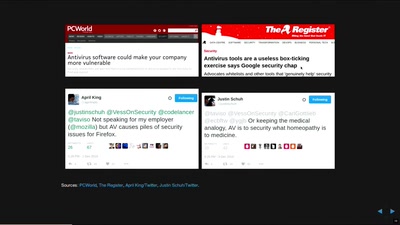
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
36 min
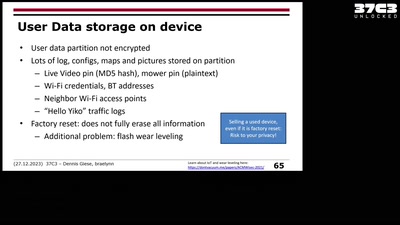
Unlocking the Road Ahead: Automotive Digital Forensics
A deep dive into an underrepresented research area
47 min
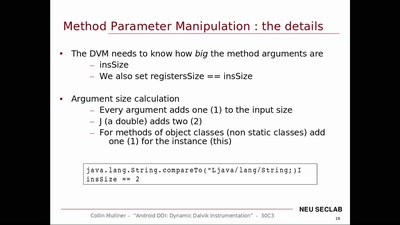
Android DDI
Dynamic Dalvik Instrumentation of Android Applications and…

60 min
i-doit: Open-Source CMDB und ITSM-Framework
IT-Dokumentation mit System

72 min
Console Hacking
Breaking the 3DS

38 min
Turning Chromebooks into regular laptops
With the power of open source!
60 min
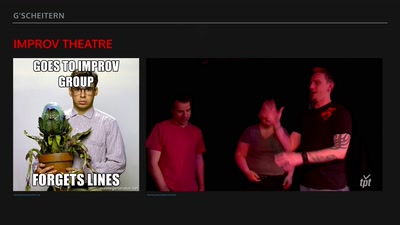
G’scheitern
The art of failure taught by improv theatre

60 min
Free Software and Hardware bring National Sovereignty
Gaza as a case study
61 min
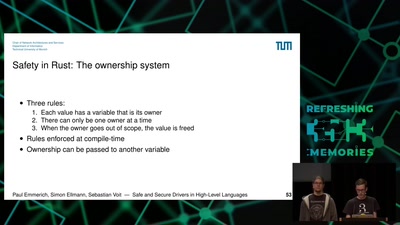
Safe and Secure Drivers in High-Level Languages
How to write PCIe drivers in Rust, go, C#, Swift, Haskell,…
53 min
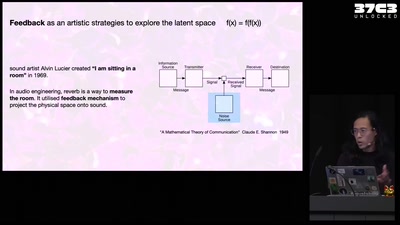
Self-cannibalizing AI
Artistic Strategies to expose generative text-to-image…
43 min