Search for "andi" returned 7497 results
65 min
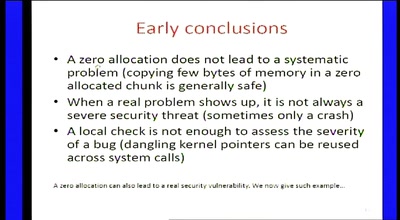
Zero-sized heap allocations vulnerability analysis
Applications of theorem proving for securing the windows…
16 min
For Fox’s Sake
Bypassing Enterprise Policy in Firefox
46 min
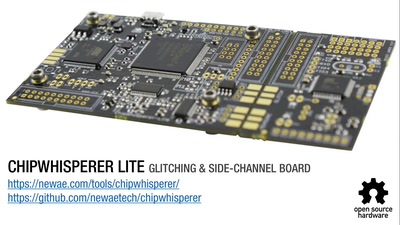
The Limits of General Purpose SDR devices
Why an SDR board like a USRP or LimeSDR is not a cellular…
38 min
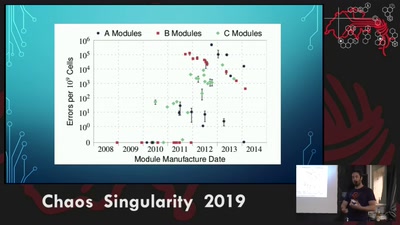
Rowhammer exploit
Viability of the Rowhammer Attack when ECC memory is used

38 min
Hardware games
How to build alternative controllers
62 min
Machine Dreams
Dreaming Machines
42 min
Wifibroadcast
How to convert standard wifi dongles into digital broadcast…
18 min
(opensource == secure)? Yes, if you audit it!
Tales in a life of a product security engineer making…
60 min