Search for "various" returned 913 results

31 min
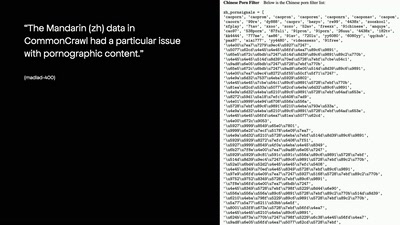
A Tale of Two Leaks:
How Hackers Breached the Great Firewall of China
95 min
Platform System Interface
Design und Evaluation holistischer Computerarchitektur
62 min
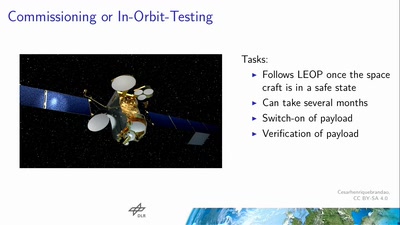
Space Ops 101
An introduction to Spacecraft Operations

58 min
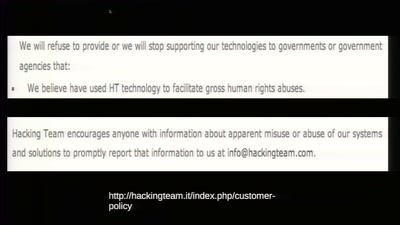
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
45 min
To Protect And Infect
The militarization of the Internet
44 min
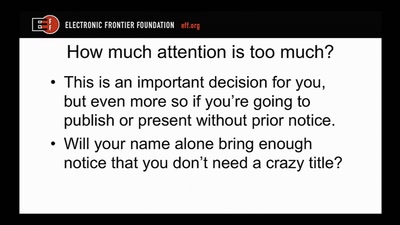
Disclosure DOs, Disclosure DON'Ts
Pragmatic Advice for Security Researchers
62 min
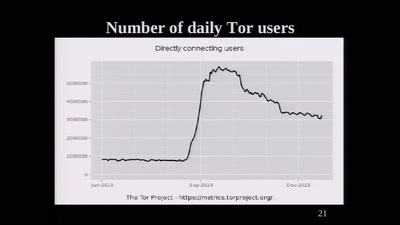
The Tor Network
We're living in interesting times
58 min
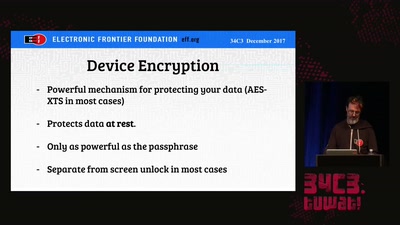
Protecting Your Privacy at the Border
Traveling with Digital Devices in the Golden Age of…
61 min
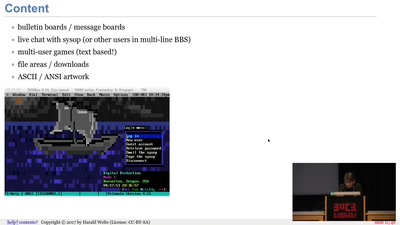
BBSs and early Internet access in the 1990ies
Modems, FIDO, Z-Netz, Usenet, UUCP, SLIP and ISDN
40 min
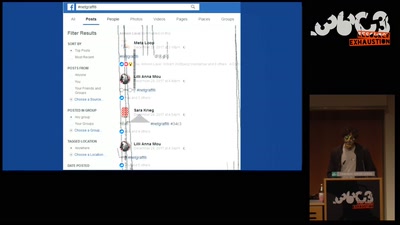
Art against Facebook
Graffiti in the ruins of the feed and the…
58 min
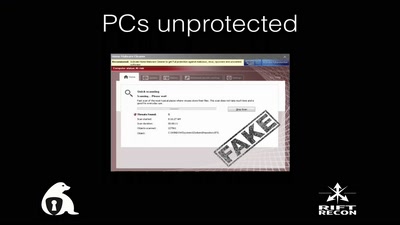
Thwarting Evil Maid Attacks
Physically Unclonable Functions for Hardware Tamper…
19 min
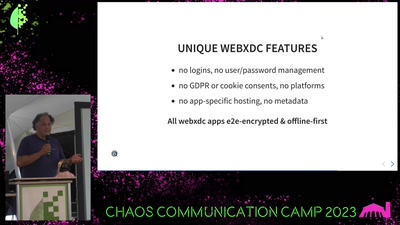
Delta Chat messenger
unlocking the potential of e-mail and the web

58 min
Operation Triangulation
What You Get When Attack iPhones of Researchers

46 min