Search for "sECuRE" returned 800 results
63 min
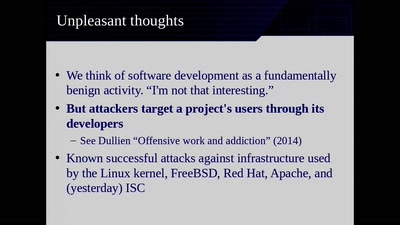
Reproducible Builds
Moving Beyond Single Points of Failure for Software…

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
57 min
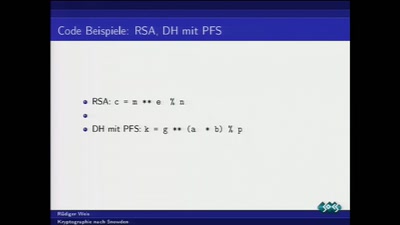
Kryptographie nach Snowden
Was tun nach der mittelmäßigen Kryptographie-Apokalypse?
62 min
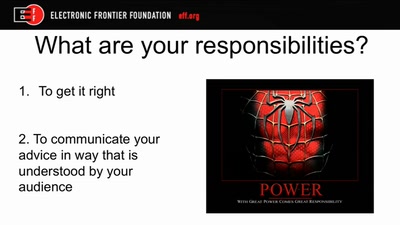
The Internet (Doesn't) Need Another Security Guide
Creating Internet Privacy and Security Resources That Don't…
66 min
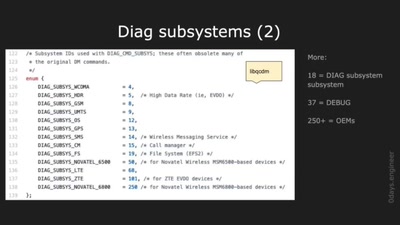
Advanced Hexagon Diag
Harnessing diagnostics for baseband vulnerability research
50 min
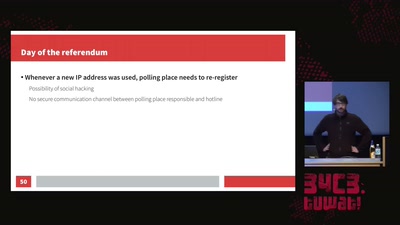
Internet censorship in the Catalan referendum
Overview of how the state censored and how it got…

55 min
The Gospel of IRMA
Attribute Based Credentials in Practice
35 min
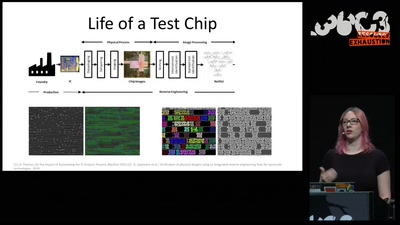
Understanding millions of gates
Introduction to IC reverse engineering for…
60 min
APT Reports and OPSEC Evolution, or: These are not the APT reports you are looking for
How advanced threat actors learn and change with innovation…
36 min
Understanding the Snooper’s Charter
Theresa May’s effort to abolish privacy

54 min
What Price the Upload Filter?
The history and costs of government exceptional access

58 min
Operation Triangulation
What You Get When Attack iPhones of Researchers
60 min
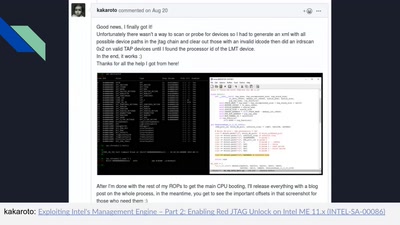
Intel Management Engine deep dive
Understanding the ME at the OS and hardware level
59 min