Search for "tim" returned 6509 results

33 min
Gone in 60 Milliseconds
Intrusion and Exfiltration in Server-less Architectures
55 min
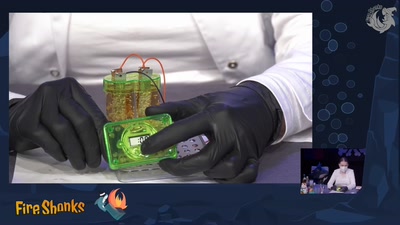
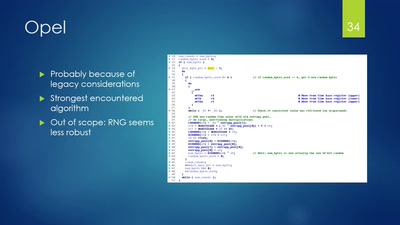
Vehicle immobilization revisited
Uncovering and assessing a second authentication mechanism…
56 min
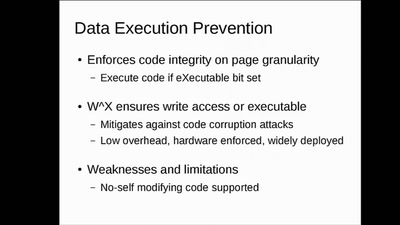
WarGames in memory
what is the winning move?
53 min
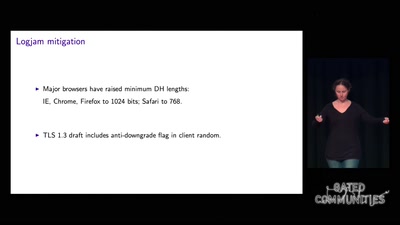
Cryptography demystified
An introduction without maths
31 min
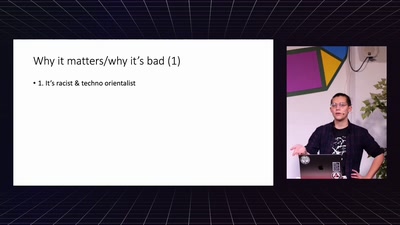
The Economic Consequences of Internet Censorship
Why Censorship is a Bad Idea for Everyone
57 min
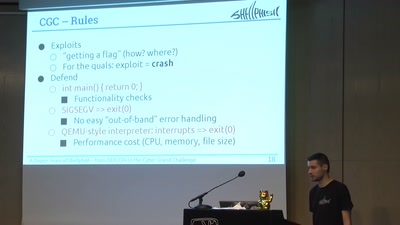
A Dozen Years of Shellphish
From DEFCON to the DARPA Cyber Grand Challenge
61 min
Code Pointer Integrity
... or how we battle the daemons of memory safety
51 min
Virtual Secure Boot
Secure Boot support in qemu, kvm and ovmf.
30 min
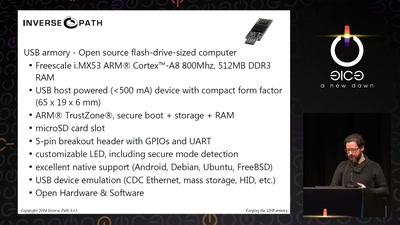
Forging the USB armory
Creating an open source secure flash-drive-sized computer
36 min
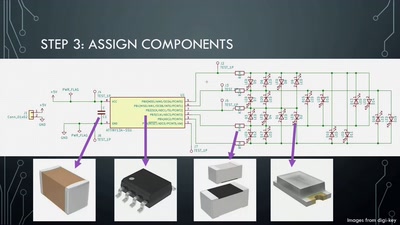
Artistic PCB Design and Fabrication
From doodle to manufacture: how I make mechanically…
29 min