Search for "JO" returned 10494 results
38 min
Unpacking the compromises of Aadhaar, and other digital identities inspired by it
Governments around the world are implementing digital…
41 min
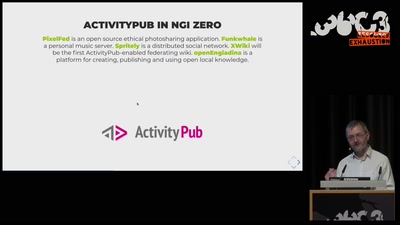
NGI Zero: A treasure trove of IT innovation
Resilient. Trustworthy. Sustainably Open.
61 min
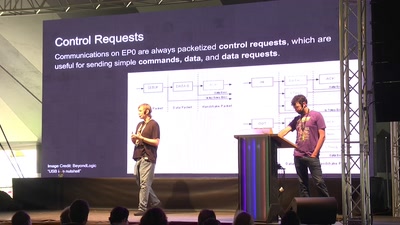
FaceDancer 2.0
easy USB hacking, sniffing, and spoofing
57 min
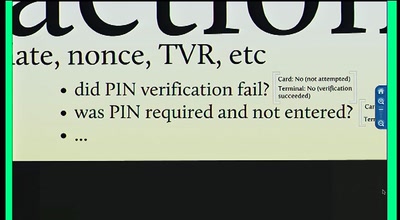
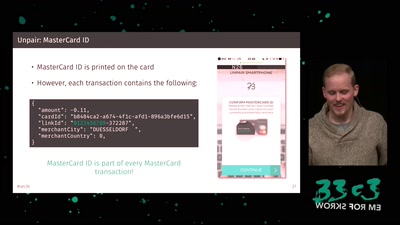
Chip and PIN is Broken
Vulnerabilities in the EMV Protocol
55 min
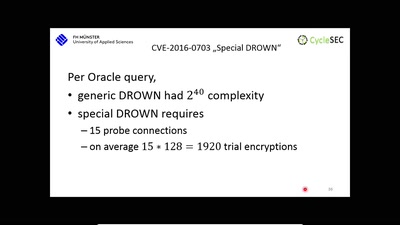
The DROWN Attack
Breaking TLS using SSLv2
50 min
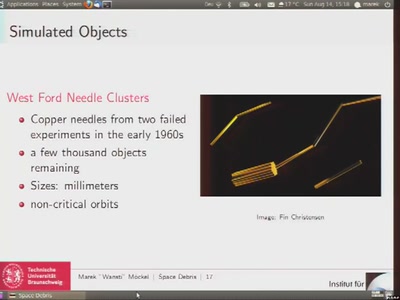
Space Debris
Simulation of orbital debris and its impacts on space travel

60 min
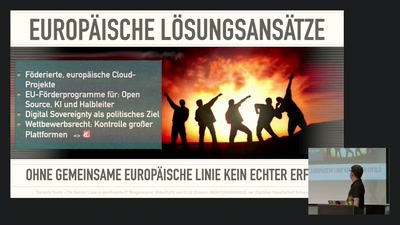
Free Software and Hardware bring National Sovereignty
Gaza as a case study
62 min
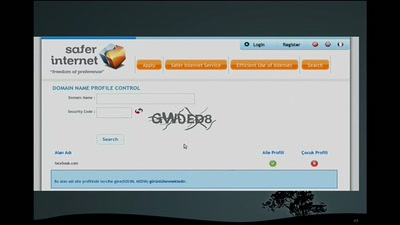
The movements against state-controlled Internet in Turkey
A short account of its history and future challenges
30 min
Shut Up and Take My Money!
The Red Pill of N26 Security
42 min
Terminator Genes and GURT - Biological Restrictions Management
Five Years after the announcement of a quasi moratorium
51 min