Search for "JO" returned 10494 results
58 min
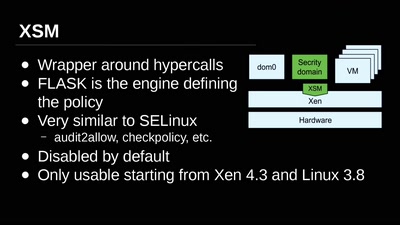
Virtual Machine Introspection
From the Outside Looking In

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
49 min
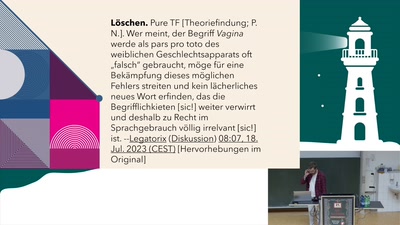
Androzentrismus in der Wikipedia
Warum die größte Wissensquelle der Welt einen male bias hat
57 min
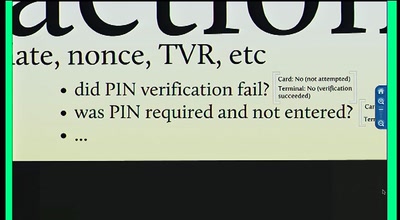
Chip and PIN is Broken
Vulnerabilities in the EMV Protocol
74 min