Search for "Jon" returned 9850 results
38 min
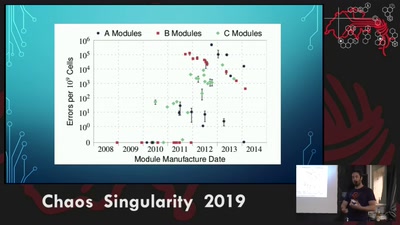
Rowhammer exploit
Viability of the Rowhammer Attack when ECC memory is used
18 min
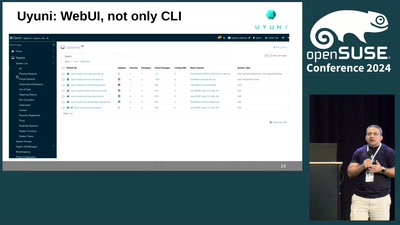
Uyuni: the open-source configuration and infrastructure management solution for…
An introduction to Uyuni
60 min
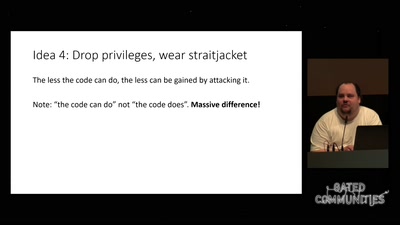
Check your privileges!
How to drop more of your privileges to reduce attack…

54 min
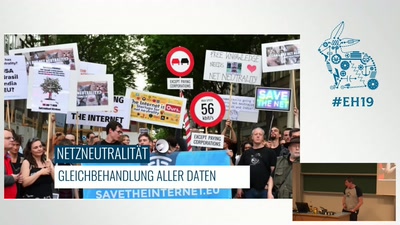
Empire and Power: The Forgotten History of the Internet as a Weapon
From the Vietnam War to Donald Trump.
54 min
Hacking Cisco Phones
Just because you are paranoid doesn't mean your phone isn't…

65 min
There's Gold in Them Circuit Boards
Why E-Waste Recycling Is Smart and How To Make It Smarter

53 min
Organisiert euch!
Wie wir voneinander lernen & zusammen wachsen

66 min
Was Bits&Bäume verbindet
Die große Eröffnung

61 min



![Fabian Schwarze: How to Gewerbeanmeldung [Freitalk N8]](https://static.media.ccc.de/media/regional/luebeck/chaotikum/52-hd.jpg)