Search for "JO" returned 10499 results

40 min
Radical Digital Painting
Fantastic Media Manipulation
73 min
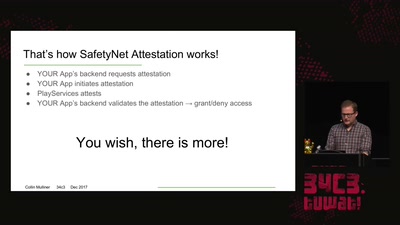
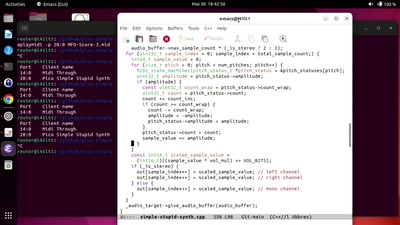
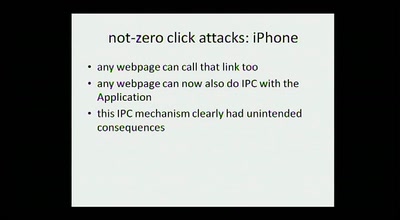
hacking smart phones
expanding the attack surface and then some
42 min
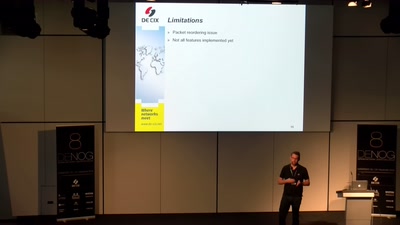
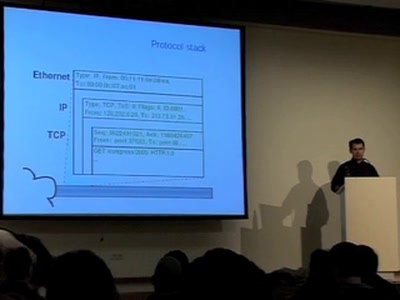
Covert channels in TCP/IP: attack and defence
Creation and detection of IP steganography for covert…
61 min
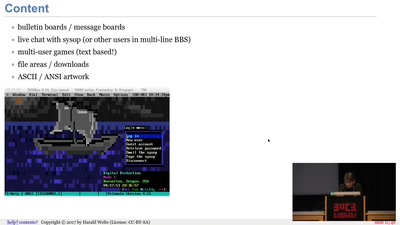
BBSs and early Internet access in the 1990ies
Modems, FIDO, Z-Netz, Usenet, UUCP, SLIP and ISDN

33 min
Authentication with Kanidm
IDM above the Sea
34 min
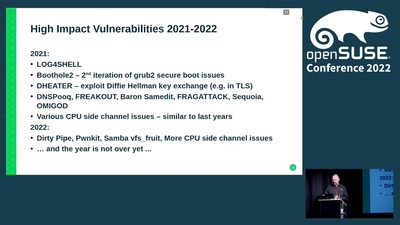
(open)SUSE Product security
a short overview
74 min
Transition Telecom
Telecommunications and networking during energy descent
43 min
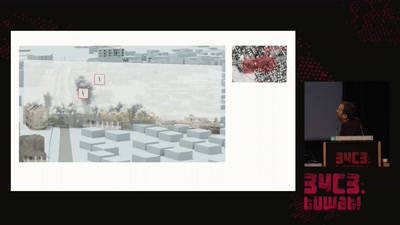
Forensic Architecture
Forensic Architecture is an independent research agency…
53 min