Search for "Thesix" returned 121 results
39 min
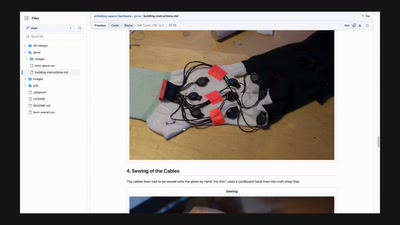
The Unfolding Space Glove
A Wearable for the Visually Impaired Translating 3D Vision…
56 min
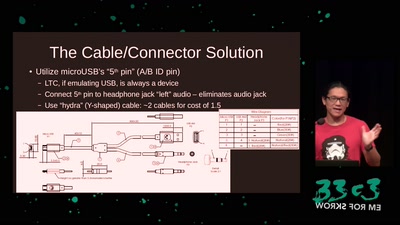
Making Technology Inclusive Through Papercraft and Sound
Introducing the Love to Code Platform
55 min
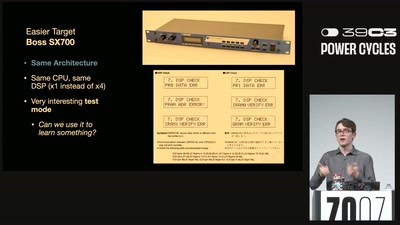
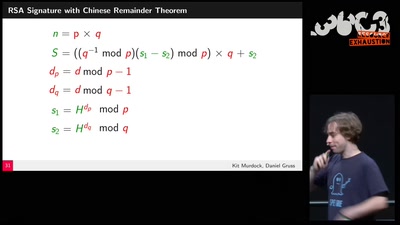
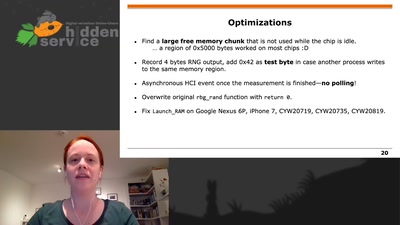
Fuzzing the phone in the iPhone
D-d-d-di-di-d-d-di-d-di-d-di-d-dimm!
57 min
“I feel like a criminal and I have to be god at the same time”
Perceptions of hackers and hacktivists on their…
54 min
Do You Think That's Funny?
Art Practice under the Regime of Anti-Terror Legislation
58 min
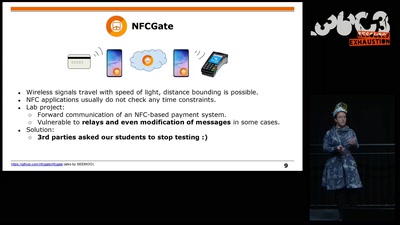
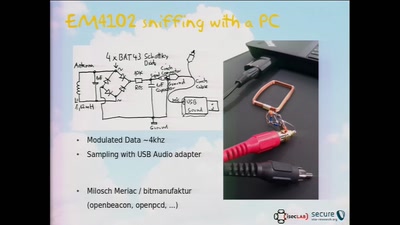
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems
95 min
Platform System Interface
Design und Evaluation holistischer Computerarchitektur
61 min
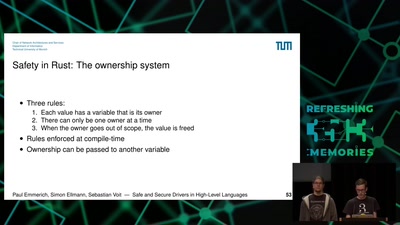
Safe and Secure Drivers in High-Level Languages
How to write PCIe drivers in Rust, go, C#, Swift, Haskell,…
58 min
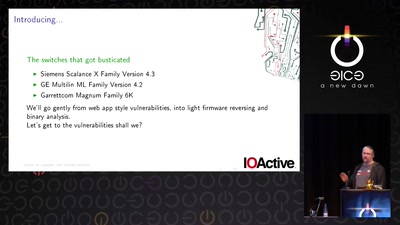
Switches Get Stitches
Industrial System Ownership
31 min