Search for "Seth Hardy" returned 901 results
62 min
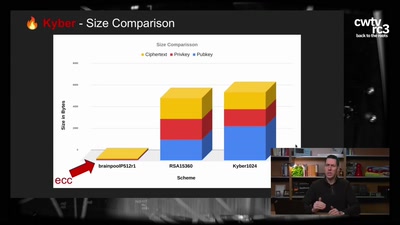
Kyber and Post-Quantum Crypto
How does it work?
31 min
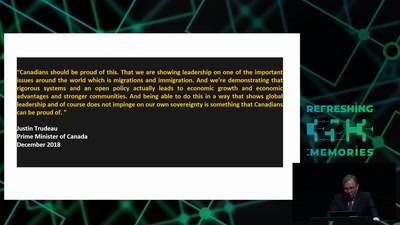
The Economic Consequences of Internet Censorship
Why Censorship is a Bad Idea for Everyone
46 min
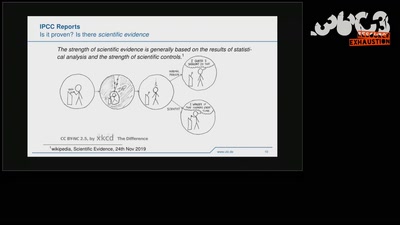
Climate Modelling
The Science Behind Climate Reports
57 min
"Fluxus cannot save the world."
What hacking has to do with avantgarde art of the 1960ies…
147 min
Hacker Jeopardy
Zahlenraten für Geeks [Number guessing for geeks]
58 min
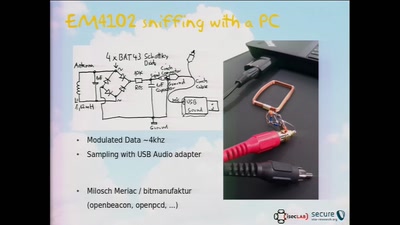
RFID Treehouse of Horror
Hacking City-Wide Access Control Systems
60 min
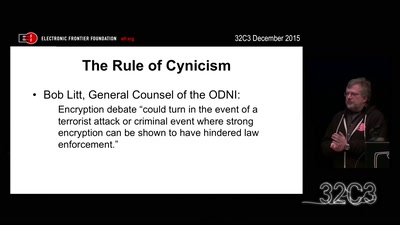
Crypto Wars Part II
The Empires Strike Back
61 min
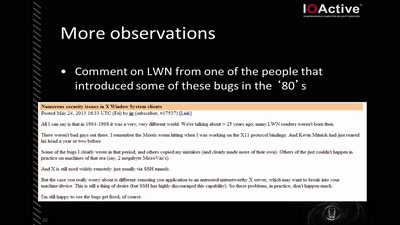
X Security
It's worse than it looks
32 min
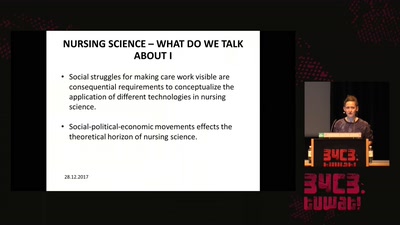
Think big or care for yourself
On the obstacles to think of emergent technologies in the…
59 min
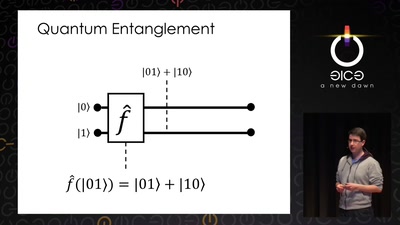
Let's build a quantum computer!
Understanding the architecture of a quantum processor
35 min
hacking disaster
mit Krisenintervention den Kapitalismus hacken
59 min
Fernvale: An Open Hardware and Software Platform, Based on the (nominally) Closed-Source…
A Lawful Method for Converting Closed IP into Open IP
33 min
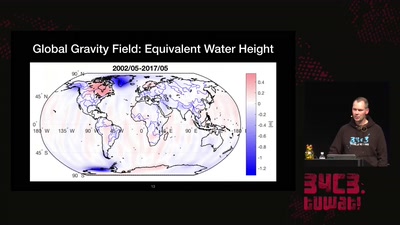
Watching the changing Earth
warning: gravity ahead
59 min
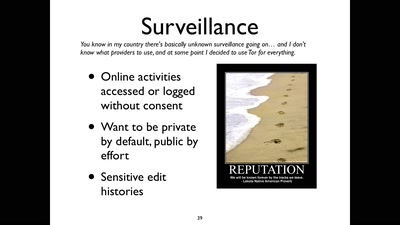
The Surveillance State limited by acts of courage and conscience
An update on the fate of the Snowden Refugees
35 min
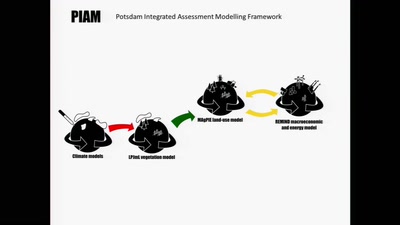
Simulating the future of the global agro-food system
Cybernetic models analyze scenarios of interactions between…

42 min