Search for "rem0te" returned 832 results
30 min
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
54 min
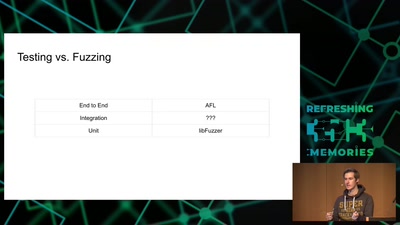
Attacking Chrome IPC
Reliably finding bugs to escape the Chrome sandbox
30 min
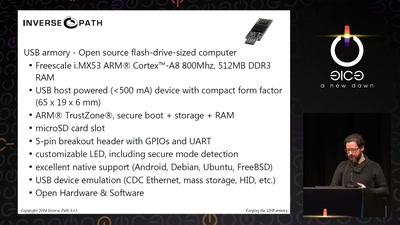
Forging the USB armory
Creating an open source secure flash-drive-sized computer
38 min
Unpacking the compromises of Aadhaar, and other digital identities inspired by it
Governments around the world are implementing digital…
42 min
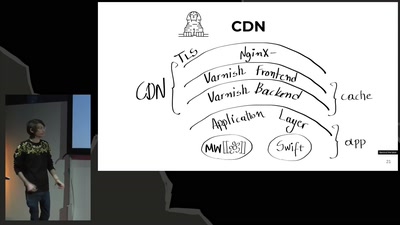
Domain Name System
Hierarchical decentralized naming system used since 30 years
61 min
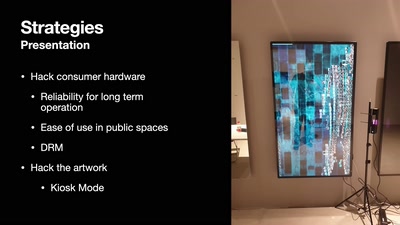
DevOps but for artworks in museums
A look into pipelines ending in museums and not in the cloud

83 min
Der Weisheit
Eine Stunde Lebenskunde - 10. Staffelfinale
46 min
What The Fax?!
Hacking your network likes it's 1980 again

53 min
Hacken Dicht
Die Aftershow-Party
43 min
Van Gogh TV - Piazza virtuale
Hallo hallo ist da jemand?
56 min
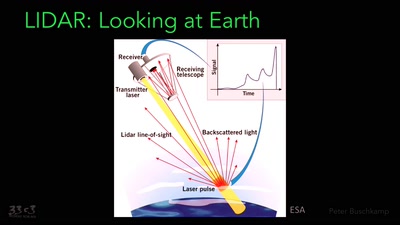
Planes and Ships and Saving Lives
How soft and hardware can play a key role in saving lives…
44 min
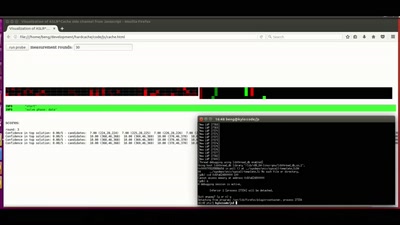
ASLR on the line
Practical cache attacks on the MMU

42 min
Union Busting
What is it and why you should care
60 min
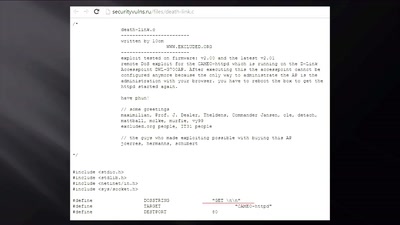
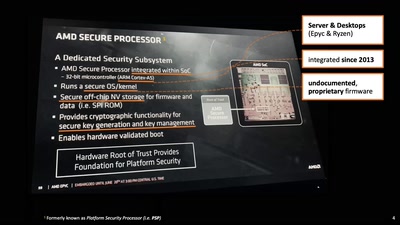
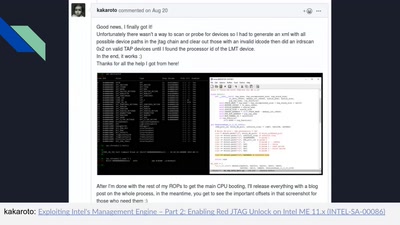
Intel Management Engine deep dive
Understanding the ME at the OS and hardware level
63 min