Search for "Leo Axt" returned 1299 results
45 min
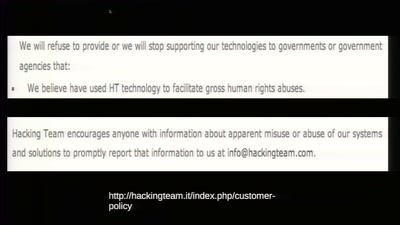
To Protect And Infect
The militarization of the Internet
35 min
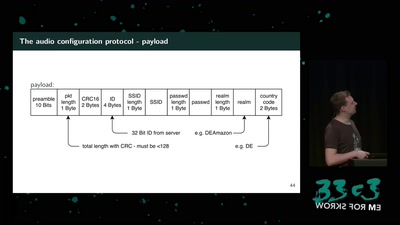
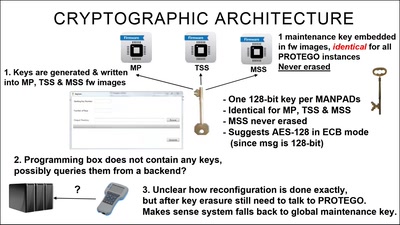
Harry Potter and the Not-So-Smart Proxy War
Taking a look at a covert CIA virtual fencing solution
42 min
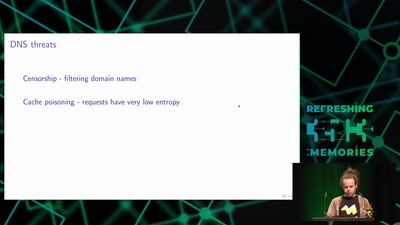
Domain Name System
Hierarchical decentralized naming system used since 30 years
61 min
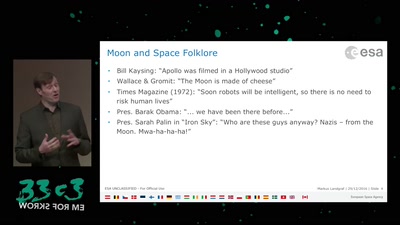
An Elevator to the Moon (and back)
Space Transportation and the Extraterrestrial Imperative

54 min
What Price the Upload Filter?
The history and costs of government exceptional access

22 min
Trust us and our business will expand!
Net-activism strategies against fake web companies
39 min
ID Cards in China: Your Worst Nightmare
In China Your ID Card Knows Everything

66 min
The Snowden Refugees under Surveillance in Hong Kong
A Rapidly Emerging Police State and Imminent Deportation to…

59 min
Security of the IC Backside
The future of IC analysis
69 min
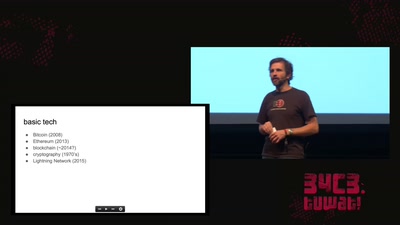
cryptocurrencies, smart contracts, etc.: revolutionary tech?
short answer: Yes!
48 min
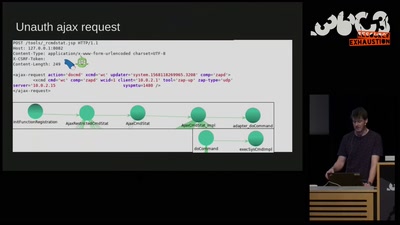
Don't Ruck Us Too Hard - Owning Ruckus AP Devices
3 different RCE vulnerabilities on Ruckus Wireless access…

45 min
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache
62 min
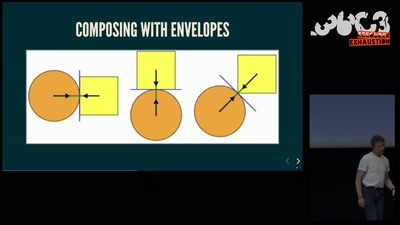
Getting software right with properties, generated tests, and proofs
Evolve your hack into robust software!

117 min
Fnord News Show
Wir helfen Euch die Fnords zu sehen.

61 min