Search for "Ben" returned 9597 results

43 min
Speaking Fiction To Power
Strategies and tactics to ‘hack’ public spaces and social…
54 min
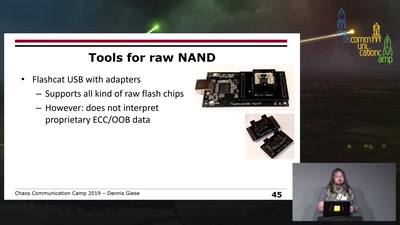
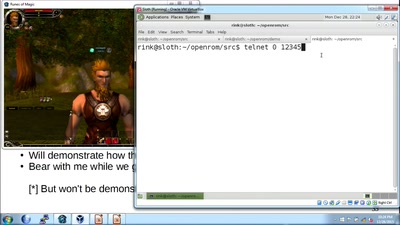
How hackers grind an MMORPG: by taking it apart!
An introduction to reverse engineering network protocols
36 min
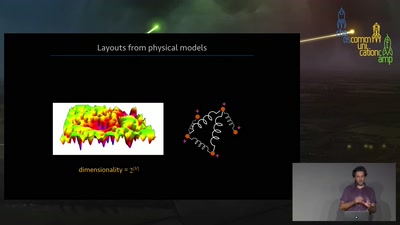
Visualization of networks using physics
How algorithms inspired by the laws of physics can create…
38 min
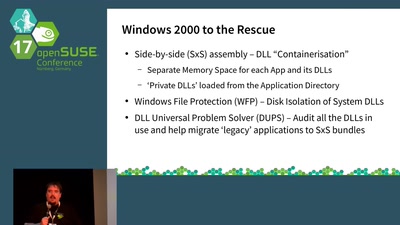
openSUSE & Jurrassic Park
What should we do about Containerised Applications?

45 min
Tech(no)fixes beware!
Spotting (digital) tech fictions as replacement for social…
87 min
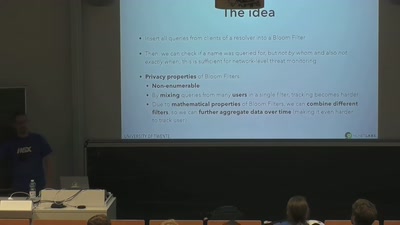
DNS privacy and security
Chaos Colloquium #1
55 min
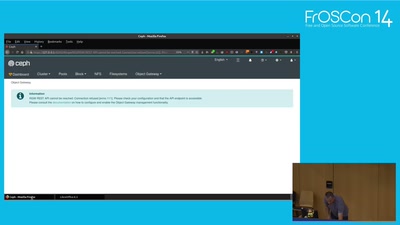
Managing and Monitoring Ceph with the Ceph Dashboard
Introduction / Overview and Demo
35 min
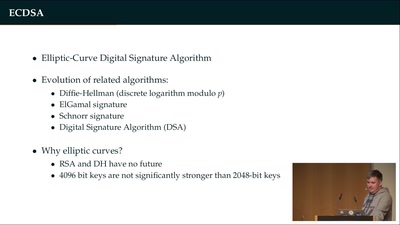
Wallet Security
How (not) to protect private keys
58 min
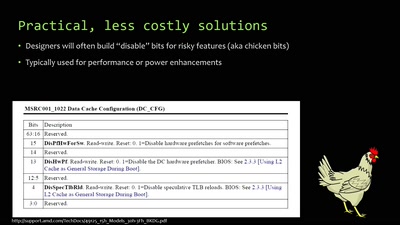
When hardware must „just work“
An inside look at x86 CPU design
45 min
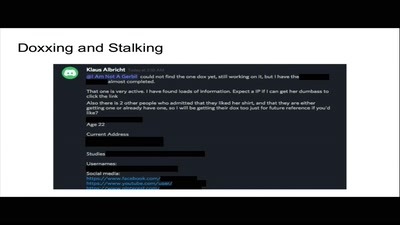
Privacy: An Unequally Distributed Resource
A Study of Privacy as Privilege in Our World
31 min
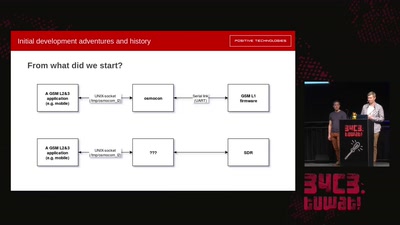
Running GSM mobile phone on SDR
SDR PHY for OsmocomBB
37 min
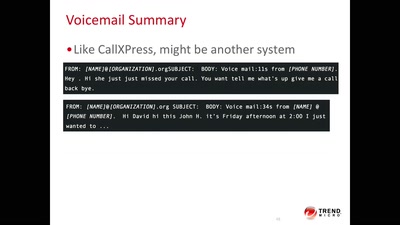
Code BROWN in the Air
A systemic update of sensitive information that you sniff…

61 min
Net Neutrality in Europe
alea iacta est
36 min