Search for "C B" returned 9732 results

87 min
Tor and China
Design of a blocking-resistant anonymity system

78 min
Stealth malware - can good guys win?
Challenges in detecting system compromises and why we’re so…

47 min
How to implement bignum arithmetic
A short look at my pet project implementation
54 min
To live outside the law you gotta be honest
Ist nicht jedes Passwort eine Manifestation des Mißtrauens?
57 min
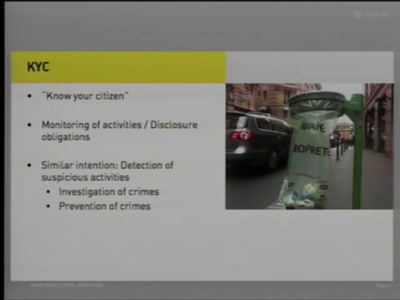
Know Your Citizens
State Authorities' Access to Sensitive Information
76 min
Information Operations
Sector-Oriented Analysis of the Potential Impact and…
46 min
The Rise and Fall of Open Source
The Million Eyeball Principle and forkbombs

64 min
Who can you trust?
Opening Ceremony and Keynote
47 min
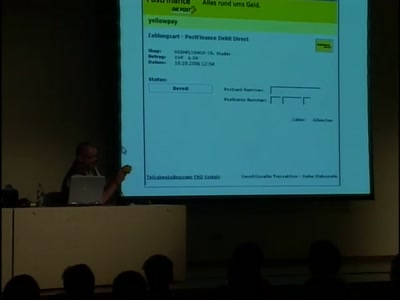
A not so smart card
How bad security decisions can ruin a debit card design

44 min
Open Source Machine Translation
From tools, to tricks, to projects: build a translation…
68 min
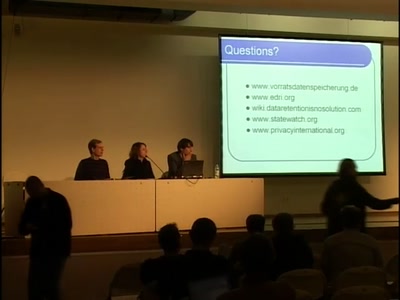
Data Retention Update
News and Perspectives on Implementation and Opposition
63 min
Transparency and Privacy
The 7 Laws of Identity and the Identity Metasystem

45 min
Introduction to matrix programming: trance codes
How to recognize trance coded communication patterns

61 min
Design and Implementation of an object-oriented, secure TCP/IP Stack
Ethereal^W Wireshark without remote exploits - a proof of…

52 min
4+2+1 Jahre BigBrotherAwards Deutschland
Eine Lesung aus dem Buch "Schwarzbuch Datenschutz"

98 min
The Grim Meathook Future
How The Tech Culture Can Maintain Relevance In The 21st…

138 min
We don't trust voting computers
The story of the dutch campaign against black-box voting to…
55 min
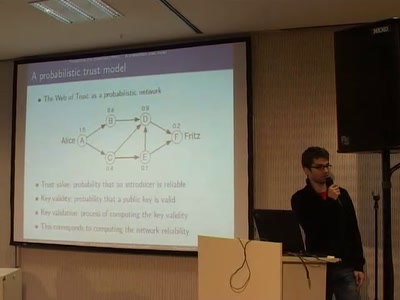
A Probabilistic Trust Model for GnuPG
A new way of evaluating a PGP web of trust by using a…
54 min
Building an Open Source PKI using OpenXPKI
Take a lot of Perl, add some OpenSSL, sprinkle it with a…

48 min
The gift of sharing
A critical approach to the notion of gift economy within…

135 min
Project Sputnik
Realtime in-building location tracking at the 23C3
61 min