Search for "*m" returned 12118 results
31 min
JODI - Apache is functioning normally
A net.art collective since 1995. Understanding the browser…
37 min
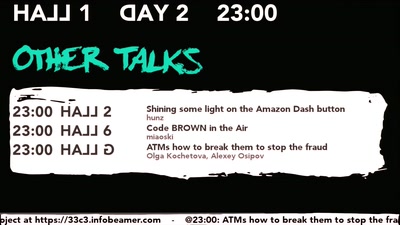
Code BROWN in the Air
A systemic update of sensitive information that you sniff…
60 min
Durchmarsch von Rechts
…und was wir dagegen tun können
40 min
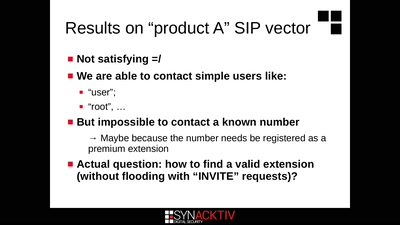
Intercoms Hacking
Call the frontdoor to install your backdoors
58 min
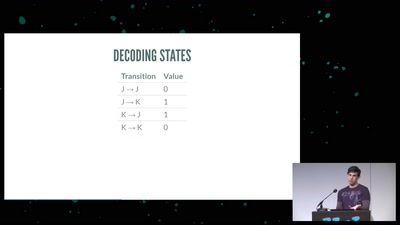
SpiegelMining – Reverse Engineering von Spiegel-Online
Wer denkt, Vorratsdatenspeicherungen und „Big Data“ sind…
64 min
On the Security and Privacy of Modern Single Sign-On in the Web
(Not Only) Attacks on OAuth and OpenID Connect
65 min
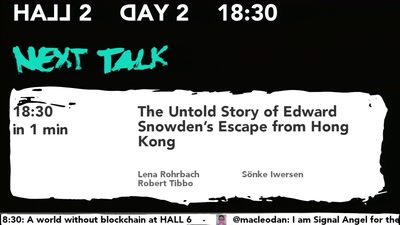
The Untold Story of Edward Snowden’s Escape from Hong Kong
and How You Can Help the Refugees Who Saved His Life
42 min
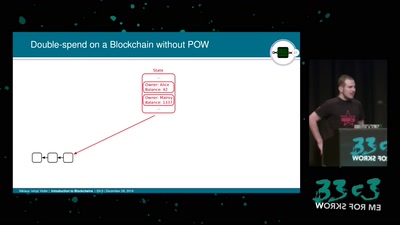
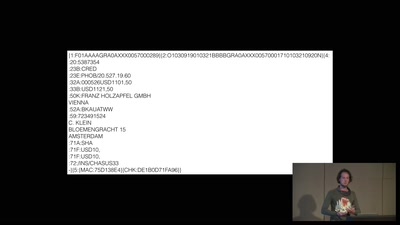
A world without blockchain
How (inter)national money transfers works
64 min
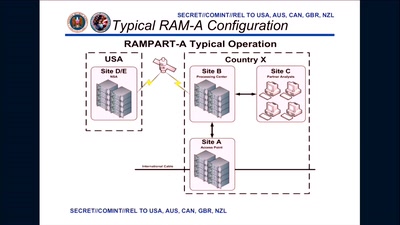
3 Years After Snowden: Is Germany fighting State Surveillance?
A Closer Look at the Political Reactions to Mass…

60 min
Hacking Reality
Mixed Reality and multi-sensory communication

61 min
Copywrongs 2.0
We must prevent EU copyright reform from breaking the…
59 min
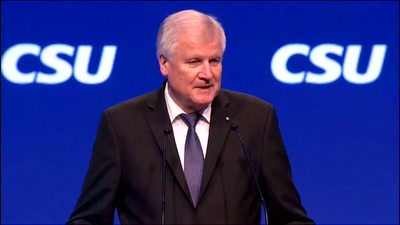
Die Sprache der Populisten
Wie politische "Gewissheiten" sprachlich konstruiert werden
57 min
No USB? No problem.
How to write an open source bit-bang low-speed USB stack…
34 min
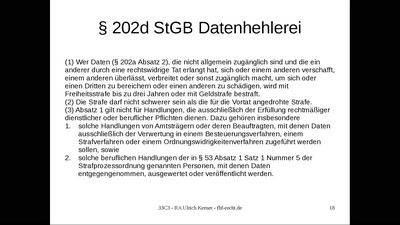
Haft für Whistleblower?
Demokratiefeindliches Strafrecht: Die Datenhehlerei gem. §…
30 min
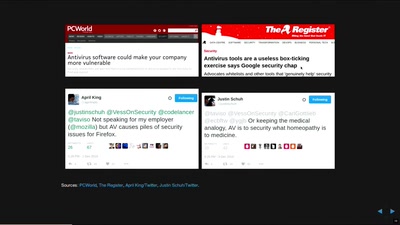
In Search of Evidence-Based IT-Security
IT security is largely a science-free field. This needs to…
36 min
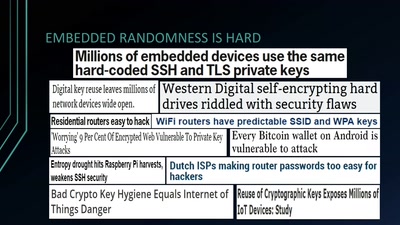
Wheel of Fortune
Analyzing Embedded OS Random Number Generators

33 min
Gone in 60 Milliseconds
Intrusion and Exfiltration in Server-less Architectures

26 min