Search for "Jong-Hoon Lee" returned 553 results

60 min
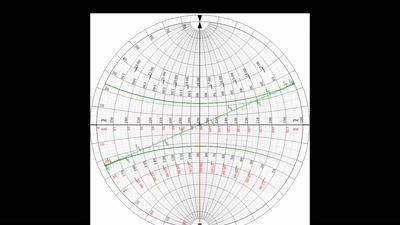
Quantum Cryptography
from key distribution to position-based cryptography
55 min
How to Build a Mind
Artificial Intelligence Reloaded
43 min
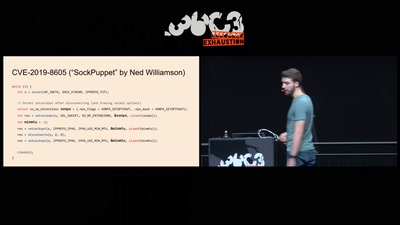
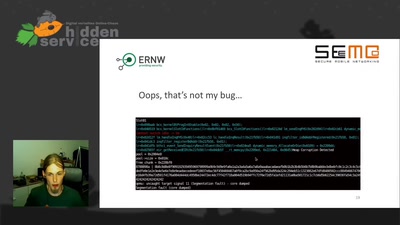
No PoC? No Fix! - A sad Story about Bluetooth Security
It is just a broken memcpy in the Bluetooth stack. Do we…

77 min
Feminist Perspectives
Inclusive and Diverse Spaces and Communities
42 min
Wifibroadcast
How to convert standard wifi dongles into digital broadcast…
59 min
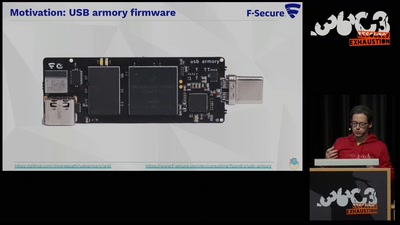
TamaGo - bare metal Go framework for ARM SoCs.
Reducing the attack surface with pure embedded Go.
44 min
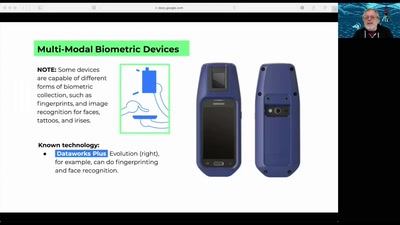
Spot the Surveillance
How to Identify Police Surveillance at Protests and Large…
46 min
You can -j REJECT but you can not hide: Global scanning of the IPv6 Internet
Finding interesting targets in 128bit of entropy
60 min