Search for "Manuel Bonk" returned 120 results
60 min
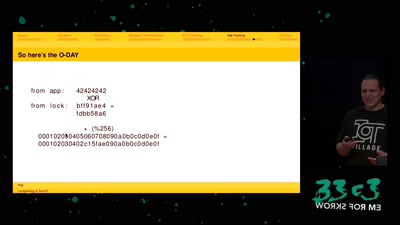
Lockpicking in the IoT
...or why adding BTLE to a device sometimes isn't smart at…
48 min
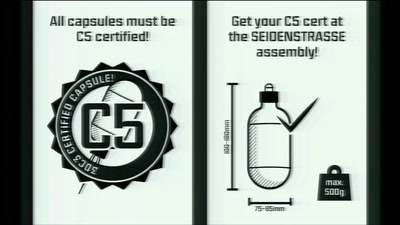
Seidenstraße
The Making of…

32 min
Finding the Weak Crypto Needle in a Byte Haystack
Automatic detection of key-reuse vulnerabilities
64 min
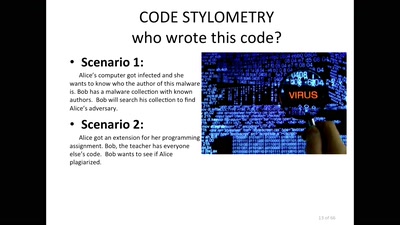
Source Code and Cross-Domain Authorship Attribution
The Role of Stylometry in Privacy

126 min
Logbuch:Netzpolitik 466
Die Ibiza-Affäre und ihre Folgen

60 min
Building a high throughput low-latency PCIe based SDR
Lessons learnt implementing PCIe on FPGA for XTRX Software…

45 min
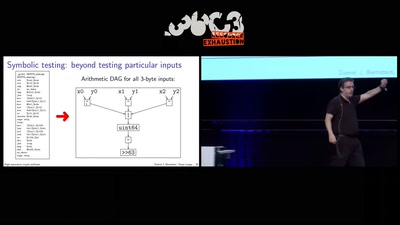
Triggering Deep Vulnerabilities Using Symbolic Execution
Deep program analysis without the headache

47 min
flow3r Badge
Frag die Teams
38 min
What your phone won’t tell you
Uncovering fake base stations on iOS devices
60 min