Search for "Paul May" returned 188 results
58 min
How risky is the software you use?
CITL: Quantitative, Comparable Software Risk Reporting
30 min
The ArduGuitar
An Arduino Powered Electric Guitar
63 min
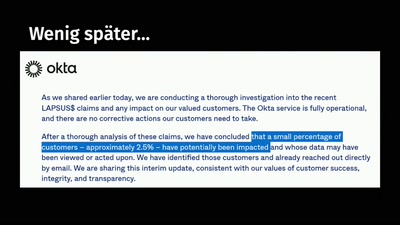
Reconstructing narratives
transparency in the service of justice
61 min
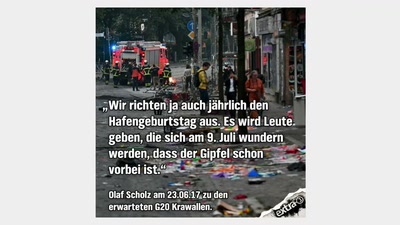
Ein Festival der Demokratie
Von Technik, Kollaborationen und Erreichtem zum G20-Gipfel…
53 min
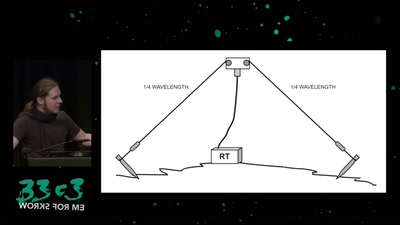
Surveilling the surveillers
About military RF communication surveillance and other…
29 min
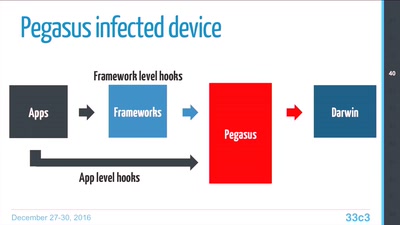
Pegasus internals
Technical Teardown of the Pegasus malware and Trident…
60 min
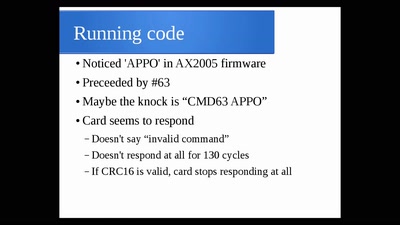
The Exploration and Exploitation of an SD Memory Card
by xobs & bunnie
109 min
Fnord-Jahresrückblick-Rückblick
20 Jahre Fnord-Jahresrückblick!
32 min
Eye Wear Computing
Augmenting the Human Mind
27 min
ANIMAL()CITY
Unleashed!
59 min
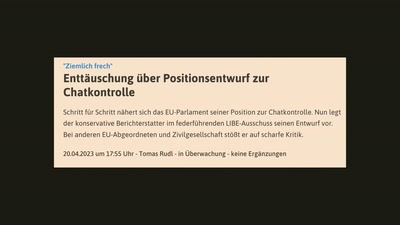
Chatkontrolle - Es ist noch nicht vorbei!
Eine Tragödie in X Akten

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice
31 min
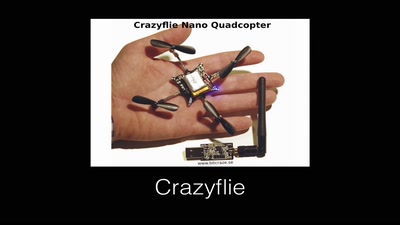
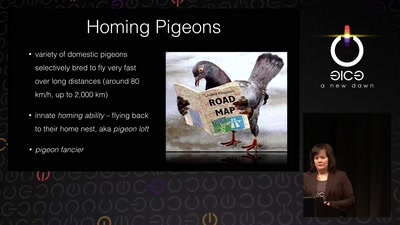
Living Drones
From war pigeons in 1914 to cyborg moths in 2014
61 min
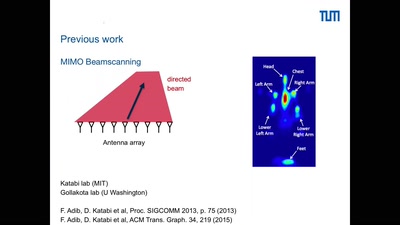
Holography of Wi-Fi radiation
Can we see the stray radiation of wireless devices? And…

59 min
Hardsploit: A Metasploit-like tool for hardware hacking
A complete toolbox for IoT security
60 min