Search for "Seth Hardy" returned 901 results

58 min
Operation Triangulation
What You Get When Attack iPhones of Researchers
64 min
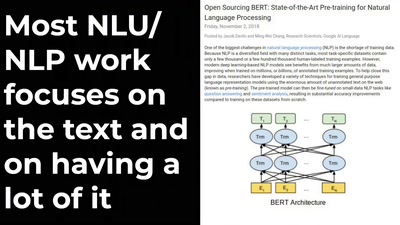
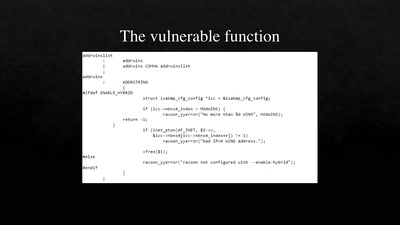
Source Code and Cross-Domain Authorship Attribution
The Role of Stylometry in Privacy
39 min
Tales of old: untethering iOS 11
Spoiler: Apple is bad at patching
61 min
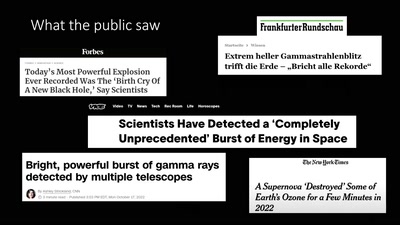
About Gamma-Ray Bursts And Boats
What We (Don't) Know About the Most Energetic Events in the…
32 min
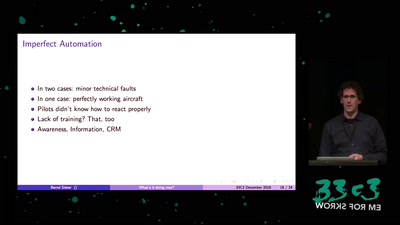
What's It Doing Now?
The Role of Automation Dependency in Aviation Accidents
32 min
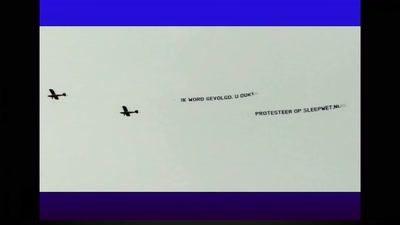
Fuck Dutch mass-surveillance: let's have a referendum!
Forcing the Netherlands to publicly debate privacy and the…
62 min
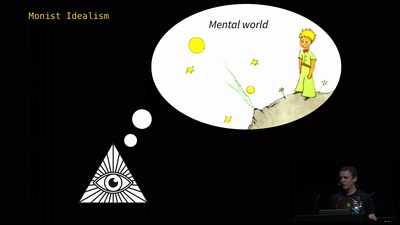
The Ghost in the Machine
An Artificial Intelligence Perspective on the Soul
56 min
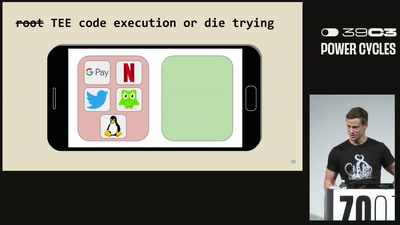
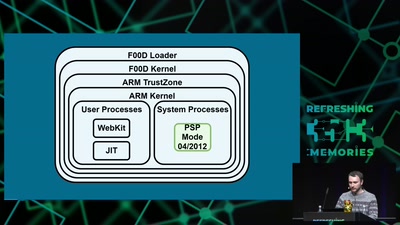
Viva la Vita Vida
Hacking the most secure handheld console
40 min
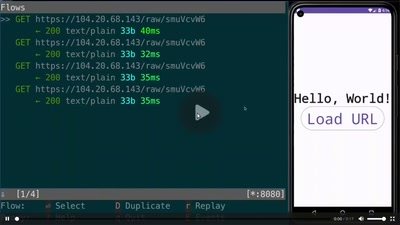
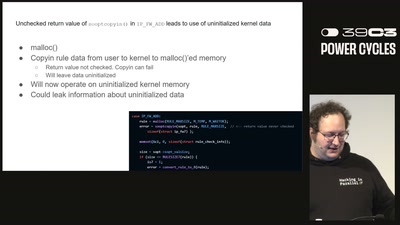
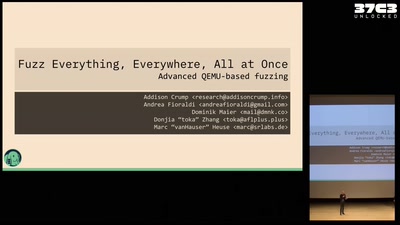
Fuzz Everything, Everywhere, All at Once
Advanced QEMU-based fuzzing
60 min
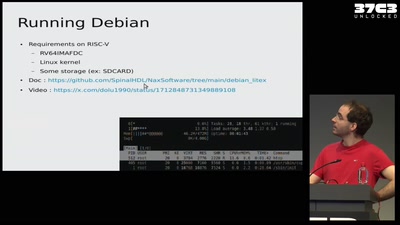
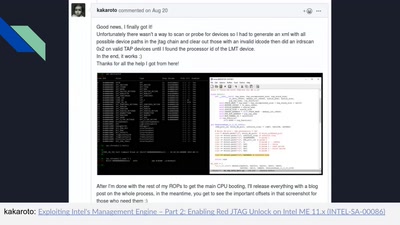
Adventures in Reverse Engineering Broadcom NIC Firmware
Unlocking a system with 100% open source firmware

60 min
What does Big Brother see, while he is watching?
Uncovering images from the secret Stasi archives.

59 min
Say hi to your new boss: How algorithms might soon control our lives.
Discrimination and ethics in the data-driven society
29 min
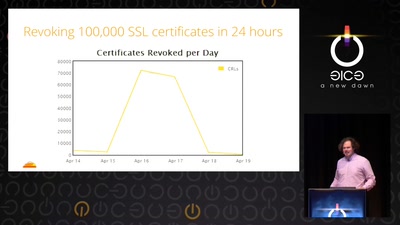
Heartache and Heartbleed: The insider’s perspective on the aftermath of Heartbleed
The untold story of what really happened, how it was…
60 min