Search for "cy" returned 6297 results

42 min
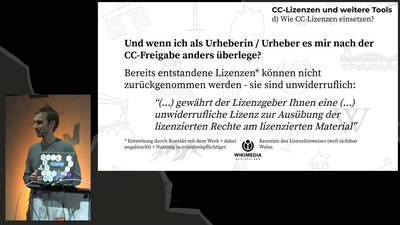
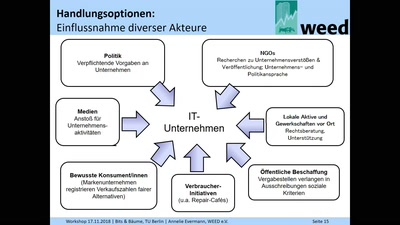
Privacy by design & remote tools
Privacy standards during the current crisis and beyond
39 min
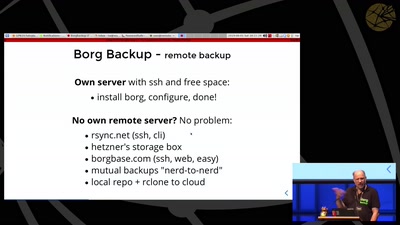
My Safe In Your House
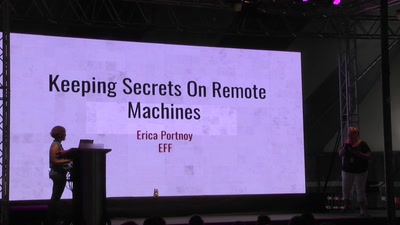
Keeping Secrets On Remote Machines
3 min
Welcome by the vice president
A few words by the vice president for research and young…
28 min
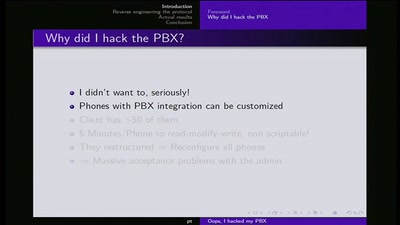
Ooops I hacked my PBX
Why auditing proprietary protocols matters

57 min
Biometric ID cards by the billion
Experiences with Aadhaar in India, or what possibly could…
42 min
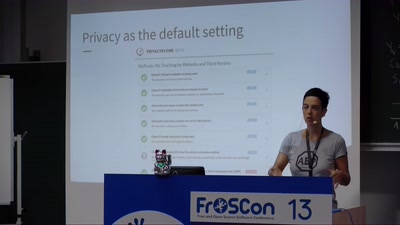
We do Privacy by Design
Best practices and real-life examples
62 min
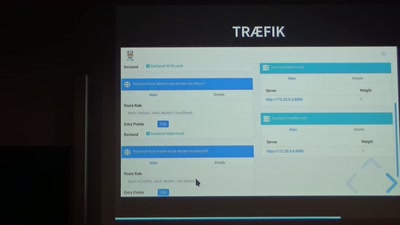
GitLab-CI und Docker Registry
Vision und Realität

25 min
Jazda: Rust on my bike
A FLOSS bike computer with Rust
29 min