Search for "sudden6" returned 106 results
60 min
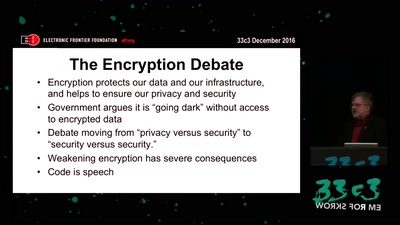
The Fight for Encryption in 2016
Crypto fight in the Wake of Apple v. FBI
58 min
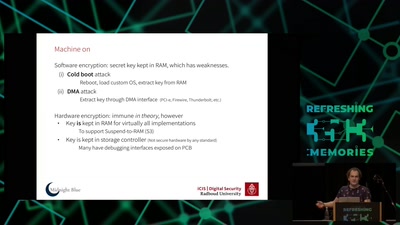
Self-encrypting deception
weaknesses in the encryption of solid state drives (SSDs)
44 min
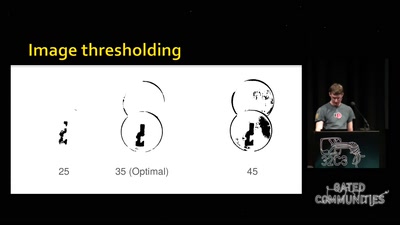
Replication Prohibited
3D printed key attacks
58 min
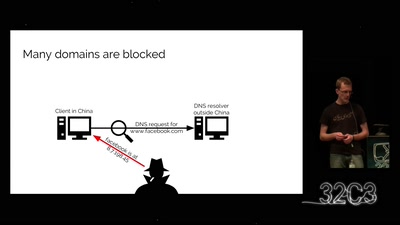
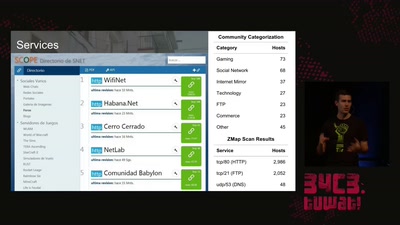
The Internet in Cuba: A Story of Community Resilience
Get a unique tour of some of the world’s most unusual…

62 min
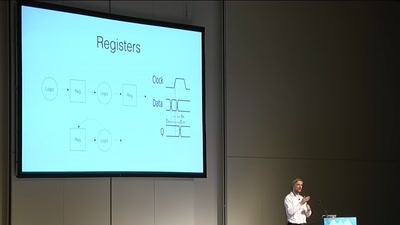
SymbiFlow - Finally the GCC of FPGAs!
A fully FOSS, Verilog to bitstream, timing driven, cross…
49 min
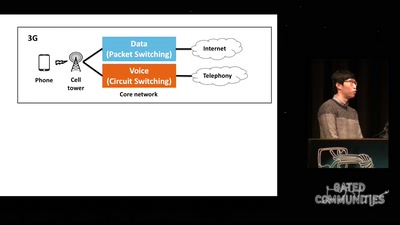
Dissecting VoLTE
Exploiting Free Data Channels and Security Problems
56 min
Deconstructing a Socialist Lawnmower
Obsolete Technologies + Critical Material Studies in Media…

37 min
Hacking (with) a TPM
Don't ask what you can do for TPMs, Ask what TPMs can do…
55 min
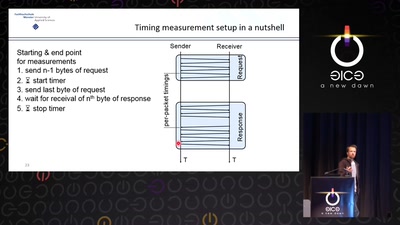
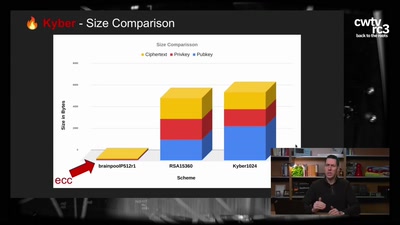
Revisiting SSL/TLS Implementations
New Bleichenbacher Side Channels and Attacks
60 min
Low Cost High Speed Photography
Using microcontrollers to capture the blink of an eye for…
91 min
What the World can learn from Hongkong
From Unanimity to Anonymity
56 min
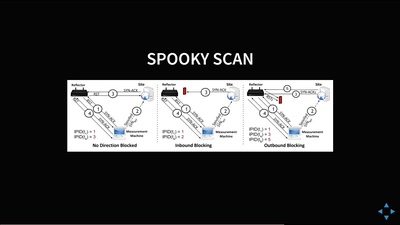
Planes and Ships and Saving Lives
How soft and hardware can play a key role in saving lives…
55 min
Inside Field Station Berlin Teufelsberg
The story of the NSA listening post – told by an ex-SIGINT…
60 min
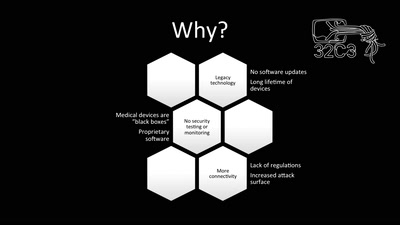
Unpatchable
Living with a vulnerable implanted device

58 min
Cyber all the Wassenaars
Export controls and exploit regulations: braindead and…
57 min
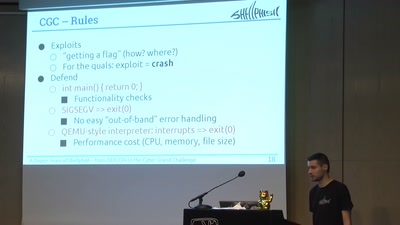
A Dozen Years of Shellphish
From DEFCON to the DARPA Cyber Grand Challenge

61 min
Copywrongs 2.0
We must prevent EU copyright reform from breaking the…
62 min
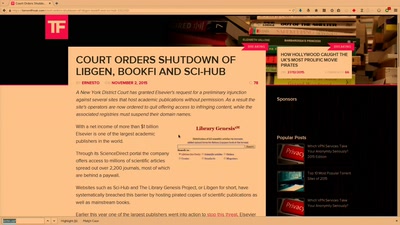
Public Library/Memory of the World
Access to knowledge for every member of society
61 min
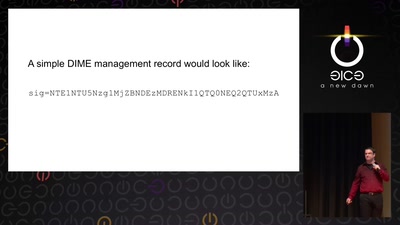
Now I sprinkle thee with crypto dust
Internet reengineering session
62 min