Search for "Elke Manz" returned 1056 results
46 min
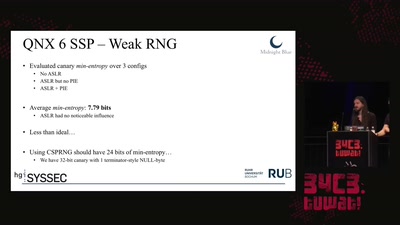
Taking a scalpel to QNX
Analyzing & Breaking Exploit Mitigations and Secure Random…
64 min
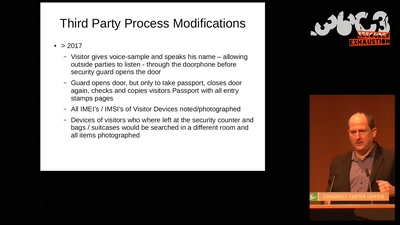
Technical aspects of the surveillance in and around the Ecuadorian embassy in London
Details about the man hunt for Julian Assange and Wikileaks
25 min
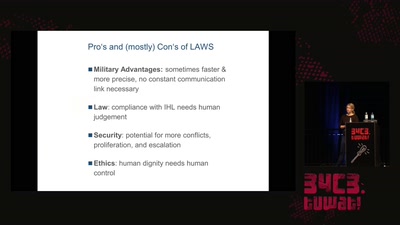
Regulating Autonomous Weapons
The time travelling android isn’t even our biggest problem
44 min
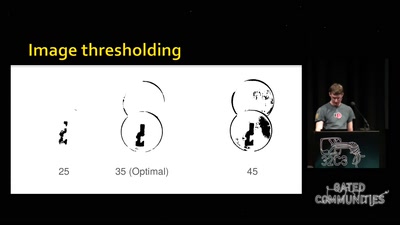
Replication Prohibited
3D printed key attacks
22 min
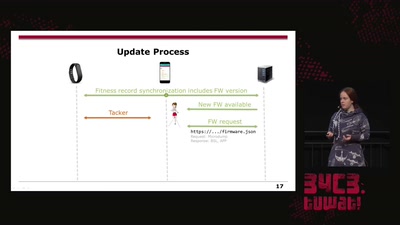
Doping your Fitbit
On Fitbit Firmware Modifications and Data Extraction
53 min
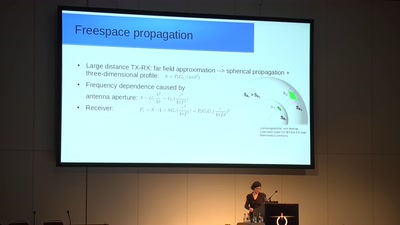
From Maxwell to antenna arrays
How 150 year old equations still help to communicate
47 min
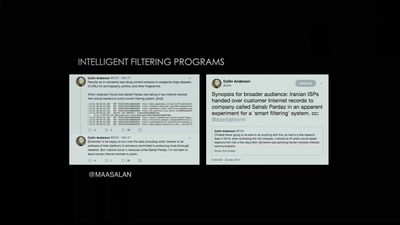
Tightening the Net in Iran
The Situation of Censorship and Surveillance in Iran, and…

59 min
Free Electron Lasers
...or why we need 17 billion Volts to make a picture.
60 min
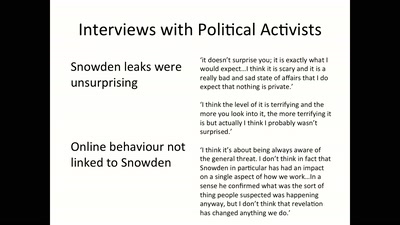
Media Coverage and the Public in the Surveillance Society
Findings from a Research Project on Digital Surveillance…

61 min
Avoiding kernel panic: Europe’s biggest fails in digital policy-making
How the institutions fuck up, and how we fuck it up as well
64 min
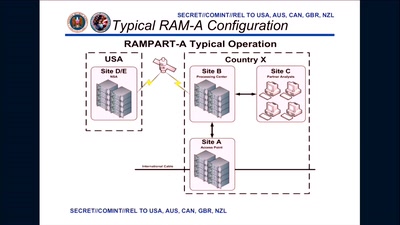
3 Years After Snowden: Is Germany fighting State Surveillance?
A Closer Look at the Political Reactions to Mass…
32 min
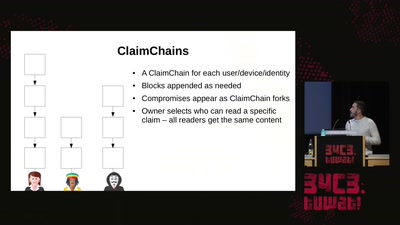
Modern key distribution with ClaimChain
A decentralized Public Key Infrastructure that supports…
41 min
Corona-Warn-App
Behind the scenes: Invisible, yet important

58 min
The Magic World of Searchable Symmetric Encryption
A brief introduction to search over encrypted data
56 min
Making Technology Inclusive Through Papercraft and Sound
Introducing the Love to Code Platform

46 min
SELECT code_execution FROM * USING SQLite;
--Gaining code execution using a malicious SQLite database
58 min
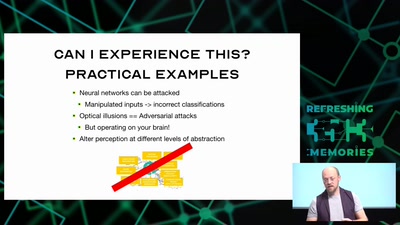
Hacking how we see
A way to fix lazy eye?
61 min