Search for "Sec" returned 2734 results
29 min
What de.fac2?
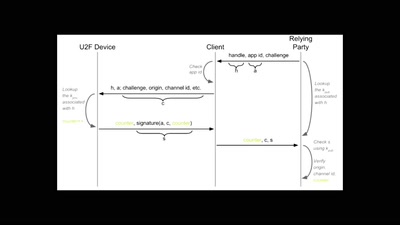
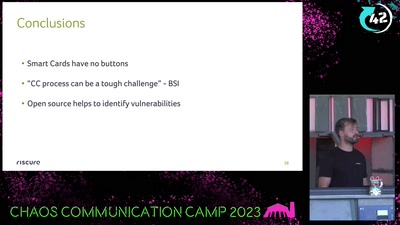
Attacking an opensource U2F device in 30 minutes or less

54 min
What Price the Upload Filter?
The history and costs of government exceptional access
62 min
Superheroes Still Need Phoneboxes
The art of making a free phonebox and the culture of…
58 min
PLC-Blaster
Ein Computerwurm für PLCs

60 min
Quantum Cryptography
from key distribution to position-based cryptography
42 min
Domain Name System
Hierarchical decentralized naming system used since 30 years
33 min
Retail Surveillance / Retail Countersurveillance
50 most unwanted retail surveillance technologies / 50 most…
61 min
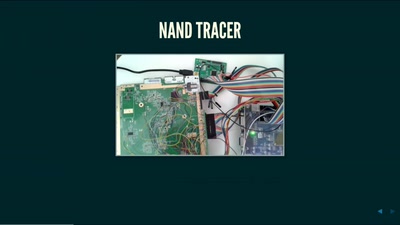
Nintendo Hacking 2016
Game Over
56 min
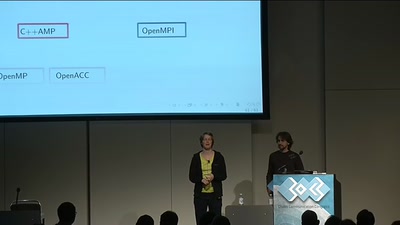
Rock' em Graphic Cards
Introduction to Heterogeneous Parallel Programming
62 min
The Ghost in the Machine
An Artificial Intelligence Perspective on the Soul
41 min
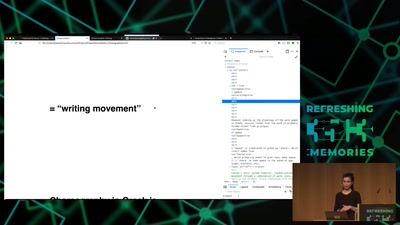
A WebPage in Three Acts
live coding performance

41 min
Extracting keys from FPGAs, OTP Tokens and Door Locks
Side-Channel (and other) Attacks in Practice

39 min
Bits and Bytes in Microgravity
Insights into the hardware and software of sounding rockets
42 min
Wifibroadcast
How to convert standard wifi dongles into digital broadcast…
40 min
Never Forgetti
a didactic live-gaming performance about dying women across…
54 min